Integrations
Integrate with Quick Connect API
The Quick Connect API allows you to easily access your data within Fortra VM, and perform tasks such as requesting data to use for reporting or integration with other security solutions.
The following instructions will help you construct your own scripts to interact with Fortra VM vulnerability data, asset data, and the vulnerability dictionary through its REST API.
Authentication
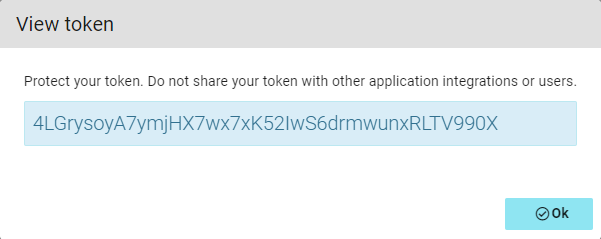
You must send each request with the API Key to authenticate your account. Additionally, each key will be valid only with the specific Fortra VM region that the account is using.
Keep this key secure as it carries the same privileges as your Fortra VM password. Do not share your secret API keys on unrestricted public areas (for example, client-side code or code repositories such as GitHub).
Generate a Fortra VM API Key
API URL
After generating your API key, determine the appropriate regional URL your key is associated with. This defines the base URL for all of your requests with this key. This is done by sending a request to the router endpoint.
The base URL may periodically change, so check the route upon each session initiation at the beginning of your script.
GET https://api.frontline.cloud/api/router/
$ curl -X GET https://api.frontline.cloud/api/router/
-k \
-H "Authorization: Token YOUR_API_TOKEN"
-X GET
{
"vm" : {,
"product" : "vm",
"url" : "https://vm.us.frontline.cloud/api/"
},
"was" : {
"product" : "was",
"url" : "https://was.us.frontline.cloud/api/"
}
}
All Fortra VM API requests begin with the The next segment of the URL path depends on the resource. For example, if your In addition to using the HTTPS protocol, all requests must include your secret API Key. The Fortra VM API returns data in JSON format. Making calls to the Fortra VM API will usually return many results. To use resources efficiently, nearly all results are paginated. The Fortra VM API implements pagination using the optional parameters count and page. Both are returned in the results as next and previous name/value pairs when applicable.Basic API usage
Data format
Pagination
Optional pagination parameters
| Parameter | Description |
|---|---|
| count |
|
| page |
|
Paginated results will include the following three name/value pairs:
Paginated results name/value pairs
| Name | Value |
|---|---|
| count | An integer value of the total number of records available. Do not confuse this with the count parameter. |
| next | The full URL string for the next page of results, if applicable, otherwise set to null. |
| previous | The full URL string for the previous page of results, if applicable, otherwise set to null. |
GET https://vm.frontline.cloud/api/scanresults/active/vulnerabilities/?count=500
{
"count" : 1768,
"next" : "https://vm.frontline.cloud/api/scanresults/active/vulnerabilities/?count=500&page=2",
"previous" : null,
"results" : [
...
...
]
}Using optional parameters
The Fortra VM API offers a rich set of optional parameters that allow you to tailor your requests. This gives you the flexibility to filter your results for specific data sets, sort your results, or use pagination as described above.
Filtering
Filter parameters must be prefixed with a count using the format of _x_. Query strings from different parameter groups can all begin with 0 (zero).
Example:
&_0_iexact_host_os_type=server&_0_eq_host_rating_ddi=F
Parameters from the same parameter set must increment their count.
Example:
&_0_iin_host_os_type=server&_1_iin_host_os_type=device&_0_eq_host_rating_ddi=F
Use the ordering parameter to sort your results. By default, the results are in ascending order by the parameter value used. Prefix the parameter’s value with a minus sign to sort descending. For example, sort ascending by title, ordering=title and sort descending by title The Python script demonstrates how to pull vulnerabilities and their associated asset data from your account.Sorting
ordering=-title.Python example of pulling data
#!/usr/bin/env python3
import urllib.request
import json
fvmUrl = "https://vm.frontline.cloud/"
apiToken = "***************************"
haveAllHosts = False
vulnData = []
requestStr = fvmUrl + "api/scanresults/active/vulnerabilities/?digest=0&count=100"
while not haveAllHosts:
# include the API token in every request you make
request = urllib.request.Request(requestStr, headers={'Authorization': 'Token ' + apiToken})
# request the data with GET
with urllib.request.urlopen(request) as response:
currentData = json.loads(response.read().decode('utf-8'))
vulnData.extend(currentData['results'])
print(f"Have {len(vulnData)} results of {currentData['count']} total")
# at the top level, the "next" variable, if present,
# gives you a complete URL where you can find the continuation
# of your request results.
if currentData.get('next') is not None:
requestStr = currentData['next']
else:
haveAllHosts = True
print(json.dumps(vulnData, indent=4, sort_keys=True))
Fortra VM Agent actions
Use these API paths to take actions on Fortra VM Agents.
Returns a list of all agents and corresponding agent IDs associated with the Fortra VM account.
$ curl -k -X GET "https://vm.frontline.cloud/api/account/1/agents/" \
-H "Content-Type: application/json;charset=utf-8" \
-H "Authorization: Token YOUR_API_TOKEN"Disables agents by their corresponding agent IDs.
$ curl -k -X PUT "https://vm.frontline.cloud/api/account/1/agents/many/" \
-H "Content-Type: application/json;charset=utf-8" \
-H "Authorization: Token YOUR_API_TOKEN" \
-d '{"items": [{"id": 1}, {"id": 2}], "value": false, "column": "active"}'Enables agents by their corresponding agent IDs.
$ curl -k -X PUT "https://vm.frontline.cloud/api/account/1/agents/many/" \
-H "Content-Type: application/json;charset=utf-8" \
-H "Authorization: Token YOUR_API-TOKEN" \
-d '{"items": [{"id": 1}, {"id": 2}], "value": true, "column": "active"}'Enables agents using agent filter and mapped operation combinations found on the Agents page filter in Fortra VM (Scan Settings > Agents).
Available mapped operations
| Mapped operation | UI operation name |
|---|---|
| contains | contains |
| inicontains | contains(or) |
| notcontains | does not contain |
| notincontains | does not contain(or) |
| iexact | is |
| notiexact | is not |
| iin | is (or) |
| notiin | is not (or) |
| lt | before |
| lte | on or before |
| gt | after |
| gte | after or before |
$ curl -k -X PUT "https://vm.frontline.cloud/api/account/1/agents/bulk/many/" \
-H "Content-Type: application/json;charset=utf-8" \
-H "Authorization: Token YOUR_API_TOKEN" \
-d '{
"filters": {
"_0_inicontains_agent_hostname": "Agent-1-b"
},
"value": true,
"column": "active"
}'Uninstalls agents using agent filter and mapped operation combinations found on the Agents page filter in Fortra VM (Scan Settings > Agents).
Available mapped operations
| Mapped operation | UI operation name |
|---|---|
| contains | contains |
| inicontains | contains(or) |
| notcontains | does not contain |
| notincontains | does not contain(or) |
| iexact | is |
| notiexact | is not |
| iin | is (or) |
| notiin | is not (or) |
| lt | before |
| lte | on or before |
| gt | after |
| gte | after or before |
$ curl -k -X PUT "https://vm.frontline.cloud/api/account/1/agents/bulk/many/" \
-H "Content-Type: application/json;charset=utf-8" \
-H "Authorization: Token YOUR_API_TOKEN" \
-d '{
"filters": {
"_0_inicontains_agent_hostname": "Agent-1-ee"
},
"value": false,
"column": "visible"
}'Uninstalls agents by their corresponding agent IDs.
$ curl -k -X PUT "https://vm.frontline.cloud/api/account/1/agents/many/" \
-H "Content-Type: application/json;charset=utf-8" \
-H "Authorization: Token YOUR_API_TOKEN" \
-d '{
"items": [{"id": 3}, {"id": 6}],
"value": false,
"column": "visible"
}'Active View assets
Use these API paths to get information about assets reconciled into Fortra VM’s Active View.
Returns a list of all assets.
Available sort parameters
| Parameter | Description |
|---|---|
| active_view_date_created | Sort list by when assets were last found (scanned). |
| active_view_date_first_created | Sort list by date assets were first found. |
| active_view_rating_ddi | Sort list by asset rating. |
| active_view_status | Sort list by asset status. |
| host_active_view_risk_score | Sort list by asset risk score. |
| host_active_view_risk_weight | Sort list by asset risk weight. |
| host_active_view_severity_ddi | Sort list by asset severity. |
| hostname | Sort list by asset hostname. |
| ip_address | Sort list by the asset IP address. |
| is_compromised | Sort list by whether an asset is compromised or not. |
| os | Sort list by the asset operating system. |
| os_type | Sort list asset OS type. |
Optional parameters
| Parameter | Description |
|---|---|
| includeAcceptableRisk | Use true or false. Default is true. Set to true to list assets with vulnerabilities that have been set as an acceptable risk within Active View. |
| includeHidden | Use true or false. Default is true. Set to true to list assets that have been hidden within Active View. |
GET https://vm.frontline.cloud/api/scanresults/active/hosts/
$ curl https://vm.frontline.cloud/api/scanresults/active/hosts/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 68,
"next" : null,
"previous" : null,
"results" : [
{
"active_view_cvss_score" : 9.3,
"active_view_date_created" : "2017-11-16T05:30:29.061147Z",
"active_view_date_first_created" : "2016-02-12T02:17:10.465288Z",
"active_view_host_id" : 919750,
"active_view_host_rating_list" : {
"ddi" : "F",
"nvd" : "High",
"pci" : "Fail"
},
"active_view_risk_score" : 375,
"active_view_risk_weight" : 75,
"active_view_security_gpa" : 0,
"active_view_status" : "matched",
"active_view_system_security_gpa" : 0,
"active_view_version" : 145729,
"active_view_vulnerability_count" : 55,
"active_view_vulnerability_severity_counts" : {
"unweighted" : {
"ddi" : {
"counts" : {
"critical" : 1,
"high" : 0,
"info" : 50,
"low" : 0,
"medium" : 2,
"none" : 0,
"trivial" : 2
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 2,
"low" : 45,
"medium" : 8
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 10,
"pass" : 45
},
"overall_security_gpa" : 0
}
},
"weighted" : {
"ddi" : {
"counts" : {
"critical" : 1,
"high" : 0,
"info" : 50,
"low" : 0,
"medium" : 2,
"none" : 0,
"trivial" : 2
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 2,
"low" : 45,
"medium" : 8
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 10,
"pass" : 45
},
"overall_security_gpa" : 0
}
}
},
"associated_webapps" : [],
"base_scan_id" : "73841_20171116T050000Z",
"date_finished" : null,
"date_started" : null,
"discovery_method" : "ping",
"dns_name" : "",
"has_notes" : true,
"hidden" : false,
"hide_from_now_on" : false,
"hostname" : "VM1WIN2008ADC",
"id" : 24503532,
"internal" : true,
"ip_address" : "172.20.97.11",
"is_compromised" : false,
"last_scanned_businessgroup" : {
"id" : 540,
"name" : "Enterprise Admins"
},
"mac_address" : "00:50:56:bc:58:d2",
"matched_status" : "matched",
"named_asset_name" : null,
"netbios_name" : "VM1WIN2008ADC",
"network_profile_id" : 126,
"network_profile_name" : "Internal Scanner Profile 2",
"notes_distribution" : {
"asset" : true,
"asset_only" : false,
"vuln_only" : false
},
"os" : "Windows Server 2008",
"os_family" : "windows",
"os_type" : "domain controller",
"partially_scanned" : false,
"pentest_status" : null,
"scan_block_id" : "158546_20171116T050000Z",
"scan_id" : "73841_20171116T050000Z",
"scan_version" : 295648,
"scan_version_active" : true,
"scan_version_cvss_score" : 9.3,
"scan_version_date_created" : "2017-11-16T05:30:29.061147Z",
"scan_version_host_id" : 24503532,
"scan_version_host_rating_list" : {
"ddi" : "F",
"nvd" : "High",
"pci" : "Fail"
},
"scan_version_host_severity_list" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
},
"scan_version_risk_score" : 375,
"scan_version_risk_weight" : 75,
"scan_version_security_gpa" : 0,
"scan_version_system_security_gpa" : 0,
"scan_version_vulnerability_count" : 55,
"scan_version_vulnerability_severity_counts" : {
"unweighted" : {
"ddi" : {
"counts" : {
"critical" : 1,
"high" : 0,
"info" : 50,
"low" : 0,
"medium" : 2,
"none" : 0,
"trivial" : 2
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 2,
"low" : 45,
"medium" : 8
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 10,
"pass" : 45
},
"overall_security_gpa" : 0
}
},
"weighted" : {
"ddi" : {
"counts" : {
"critical" : 1,
"high" : 0,
"info" : 50,
"low" : 0,
"medium" : 2,
"none" : 0,
"trivial" : 2
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 2,
"low" : 45,
"medium" : 8
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 10,
"pass" : 45
},
"overall_security_gpa" : 0
}
}
},
"scanner_version" : "2.2.70.1"
},
...
...
]
}Returns a single asset for the given <id>.
GET https://vm.frontline.cloud/api/scanresults/active/hosts/<id>/
$ curl https://vm.frontline.cloud/api/scanresults/active/hosts/24503532/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"active_view_cvss_score" : 9.3,
"active_view_date_created" : "2017-11-16T05:30:29.061147Z",
"active_view_date_first_created" : "2016-02-12T02:17:10.465288Z",
"active_view_host_id" : 919750,
"active_view_host_rating_list" : {
"ddi" : "F",
"nvd" : "High",
"pci" : "Fail"
},
"active_view_host_severity_list" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
},
"active_view_risk_score" : 375,
"active_view_risk_weight" : 75,
"active_view_scanner_versions" : "2.2.47.2,2.2.51.0,...,2.2.70.1",
"active_view_security_gpa" : 0,
"active_view_services_list" : [
{
"port" : 53,
"protocol" : "dns",
"scan_vulnerability_count" : 0,
"transport" : "tcp",
"tunnel" : "none"
},
...
...
],
"active_view_status" : "matched",
"active_view_system_security_gpa" : 0,
"active_view_version" : 145729,
"active_view_vuln_tag_list" : [
{
"codename" : "administration",
"color" : null,
"id" : 2307,
"name" : "administration",
"tagged_by" : "system"
},
...
...
],
"active_view_vulnerability_count" : 55,
"active_view_vulnerability_severity_counts" : {
"unweighted" : {
"ddi" : {
"counts" : {
"critical" : 1,
"high" : 0,
"info" : 50,
"low" : 0,
"medium" : 2,
"none" : 0,
"trivial" : 2
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 2,
"low" : 45,
"medium" : 8
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 10,
"pass" : 45
},
"overall_security_gpa" : 0
}
},
"weighted" : {
"ddi" : {
"counts" : {
"critical" : 1,
"high" : 0,
"info" : 50,
"low" : 0,
"medium" : 2,
"none" : 0,
"trivial" : 2
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 2,
"low" : 45,
"medium" : 8
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 10,
"pass" : 45
},
"overall_security_gpa" : 0
}
}
},
"associated_webapps" : [],
"base_scan_id" : "73841_20171116T050000Z",
"date_finished" : null,
"date_started" : null,
"discovery_method" : "ping",
"dns_name" : "",
"has_notes" : true,
"hidden" : false,
"hide_from_now_on" : false,
"host_tag_list" : [
{
"codename" : "administration",
"color" : null,
"id" : 2307,
"name" : "administration",
"tagged_by" : "system"
},
...
...
],
"hostname" : "VM1WIN2008ADC",
"id" : 24503532,
"internal" : true,
"ip_address" : "172.20.97.11",
"is_compromised" : false,
"last_scanned_businessgroup" : {
"id" : 540,
"name" : "Enterprise Admins"
},
"mac_address" : "00:50:56:bc:58:d2",
"matched_status" : "matched",
"named_asset_name" : null,
"netbios_name" : "VM1WIN2008ADC",
"network_profile_id" : 126,
"network_profile_name" : "Internal Scanner Profile 2",
"notes_distribution" : {
"asset" : false,
"asset_only" : false,
"vuln_only" : false
},
"os" : "Windows Server 2008",
"os_family" : "windows",
"os_type" : "domain controller",
"parent_ip_address" : "172.20.97.11",
"partially_scanned" : false,
"pentest_status" : null,
"rna" : {
"name" : null,
"proxy_port" : null
},
"scan_block_id" : "158546_20171116T050000Z",
"scan_id" : "73841_20171116T050000Z",
"scan_version" : 295648,
"scan_version_active" : true,
"scan_version_cvss_score" : 9.3,
"scan_version_date_created" : "2017-11-16T05:30:29.061147Z",
"scan_version_host_id" : 24503532,
"scan_version_host_rating_list" : {
"ddi" : "F",
"nvd" : "High",
"pci" : "Fail"
},
"scan_version_host_severity_list" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
},
"scan_version_risk_score" : 375,
"scan_version_risk_weight" : 75,
"scan_version_scanner_versions" : "2.2.70.1",
"scan_version_security_gpa" : 0,
"scan_version_services_list" : [
{
"port" : 53,
"protocol" : "dns",
"scan_vulnerability_count" : 0,
"transport" : "tcp",
"tunnel" : "none"
},
...
...
],
"scan_version_system_security_gpa" : 0,
"scan_version_vulnerability_count" : 55,
"scan_version_vulnerability_severity_counts" : {
"unweighted" : {
"ddi" : {
"counts" : {
"critical" : 1,
"high" : 0,
"info" : 50,
"low" : 0,
"medium" : 2,
"none" : 0,
"trivial" : 2
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 2,
"low" : 45,
"medium" : 8
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 10,
"pass" : 45
},
"overall_security_gpa" : 0
}
},
"weighted" : {
"ddi" : {
"counts" : {
"critical" : 1,
"high" : 0,
"info" : 50,
"low" : 0,
"medium" : 2,
"none" : 0,
"trivial" : 2
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 2,
"low" : 45,
"medium" : 8
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 10,
"pass" : 45
},
"overall_security_gpa" : 0
}
}
},
"scanner_version" : "2.2.70.1",
"tag_list" : [
{
"codename" : "administration",
"color" : null,
"id" : 2307,
"name" : "administration",
"tagged_by" : "system"
},
...
...
],
"vuln_tag_list" : [
{
"codename" : "administration",
"color" : null,
"id" : 2307,
"name" : "administration",
"tagged_by" : "system"
},
...
...
]
}Returns a list of vulnerabilities detected for a given asset <id>.
GET https://vm.frontline.cloud/api/scanresults/active/hosts/<id>/vulnerabilities/
$ curl https://vm.frontline.cloud/api/scanresults/active/hosts/24503532/vulnerabilities/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 55,
"next" : "https://vm.frontline.cloud/api/scanresults/active/hosts/24503532/vulnerabilities/?page=2",
"previous" : null,
"results" : [
{
"acceptable_risk" : true,
"active_view_date_created" : "2017-11-16T05:30:29.061147Z",
"active_view_date_first_created" : "2017-04-20T04:06:42.056220Z",
"active_view_host_id" : 919750,
"active_view_status" : "recurred",
"active_view_version" : 145729,
"cvss_score" : "9.3",
"data" : "This asset is missing the MS17-010 patch.\n\nVulnerable Response:\n ff 53 4d 42 25 05 02 00 c0 88 01 44 00 10 00 00 .SMB%......D....\n 00 00 00 00 00 00 00 00 05 80 06 00 00 08 6d 42 ..............mB\n 00 00 00 ...\n",
"date_finished" : null,
"date_started" : null,
"detect_type" : "remote",
"false_positive" : false,
"has_notes" : true,
"hidden" : false,
"hide_from_now_on" : false,
"host_hidden" : false,
"host_id" : 24503532,
"hostname" : "VM1WIN2008ADC",
"id" : 957098082,
"id_ddi" : 122051,
"ip_address" : "172.20.97.11",
"manually_added" : false,
"manually_added_fix_status_name" : null,
"matched_status" : "recurred",
"port" : 445,
"protocol" : "smb",
"scan_block_id" : "158546_20171116T050000Z",
"scan_id" : "73841_20171116T050000Z",
"scanner_version" : "2.2.70.1",
"severities" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
},
"tag_list" : [
{
"codename" : "moderate to fix",
"color" : null,
"id" : 2304,
"name" : "moderate to fix",
"tagged_by" : "system"
},
...
...
],
"title" : "MS17-010: SMB Remote Code Execution Vulnerability (Network Check)",
"transport" : "tcp",
"tunnel" : "none",
"vuln_class" : "explicit"
},
...
...
]
}Returns the notes created for a given asset <id>.
GET https://vm.frontline.cloud/api/scanresults/active/hosts/<id>/notes/
$ curl https://vm.frontline.cloud/api/scanresults/active/hosts/24503532/notes/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
[
{
"account_user_account_id" : 115,
"account_user_email" : "barney.rubble@flintstone.com",
"account_user_id" : 7703,
"account_user_name" : "Barney Rubble",
"date_created" : "2018-04-05T18:31:41.021941Z",
"date_modified" : "2018-04-05T18:31:41.021986Z",
"host_id" : 24503532,
"id" : 1232597,
"id_ddi" : null,
"note_group_id" : 1232597,
"note_original_author" : {
"account_user_email" : "barney.rubble@flintstone.com",
"account_user_fullname" : "Barney Rubble",
"account_user_id" : 7703
},
"note_type" : "client",
"note_type_name" : "Client",
"order_number" : 0,
"scan_id" : "73841_20171116T050000Z",
"scan_name" : "Daily Assessment",
"scan_vulnerability_id" : null,
"target" : {
"data" : {
"hostname" : "VM1WIN2008ADC",
"ip_address" : "172.20.97.11"
},
"type" : "asset"
},
"ticket_metadata" : null,
"title" : null,
"value" : "For Win Team in Chicago to remediate.",
"version" : 1
}
]Active View vulnerabilities
Use these API paths to get information about vulnerabilities reconciled into Fortra VM’s Active View.
Returns a list of all vulnerabilities.
Available sort parameters
| Parameter | Description |
|---|---|
| scan_vulnerability_count | Sort list by the total number of vulnerability instances per vulnerability. |
| severity_ddi | Sort list by vulnerability severity. |
| title | Sort list by vulnerability title. |
Optional parameters
| Parameter | Description |
|---|---|
| digest | Use true or false. Default is false. Set to true to list vulnerabilities in a condensed format, grouping vulnerabilities by id_ddi instead of showing each instance. |
| includeAcceptableRisk | Use true or false. Default is false. Set to true to list vulnerabilities that have been set as an acceptable risk within Active View. |
| includeFixed | Use true or false. Default is false. Set to true to list vulnerabilities that have been fixed. |
| includeHidden | Use true or false. Default is false. Set to true to list vulnerabilities that have been hidden within Active View. |
GET https://vm.frontline.cloud/api/scanresults/active/vulnerabilities/?digest=true
$ curl https://vm.frontline.cloud/api/scanresults/active/hosts/24503532/notes/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 135,
"next" : "https://vm.frontline.cloud/api/scanresults/active/vulnerabilities/?count=3&digest=true&ordering=-severity_ddi&page=2",
"previous" : null,
"results" : [
{
"hidden" : false,
"id_ddi" : 122051,
"matched_change" : {
"change" : -1,
"current" : 22,
"diff" : 22,
"fixed" : 0,
"new" : 1,
"recurred" : 21
},
"scan_vulnerability_count" : 22,
"severities" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
},
"title" : "MS17-010: SMB Remote Code Execution Vulnerability (Network Check)",
"vuln_class" : "explicit"
},
{
"hidden" : false,
"id_ddi" : 113790,
"matched_change" : {
"change" : 0,
"current" : 8,
"diff" : 8,
"fixed" : 0,
"new" : 0,
"recurred" : 8
},
"scan_vulnerability_count" : 8,
"severities" : {
"ddi" : "critical",
"nvd" : "medium",
"pci" : "fail"
},
"title" : "SSL Connection: Server Vulnerable to Heartbleed Attack",
"vuln_class" : "explicit"
},
{
"hidden" : false,
"id_ddi" : 104433,
"matched_change" : {
"change" : 0,
"current" : 1,
"diff" : 1,
"fixed" : 0,
"new" : 0,
"recurred" : 1
},
"scan_vulnerability_count" : 1,
"severities" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
},
"title" : "HTTP Easily Guessable Credentials",
"vuln_class" : "explicit"
}
]
}Returns the vulnerability details for a single vulnerability using the vulnerability’s <id_ddi>.
GET https://vm.frontline.cloud/api/scanresults/active/vulnerabilities/?_0_eq_vuln_id_ddi=<id_ddi>
$ curl https://vm.frontline.cloud/api/scanresults/active/vulnerabilities/?_0_eq_vuln_id_ddi=104433 \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 1,
"next" : null,
"previous" : null,
"results" : [
{
"acceptable_risk" : null,
"active_view_date_created" : "2018-03-27T21:00:03.678341Z",
"active_view_date_first_created" : "2018-03-12T22:53:12.586355Z",
"active_view_host_id" : 30617403,
"active_view_status" : "recurred",
"active_view_version" : 179970,
"cvss_score" : "10.0",
"data" : "Authentication Successful In Forms:\n172.20.71.98:81:\n\t/admin/index.php?page=login : /admin/index.php?page=login:\n\t\tadmin:admin\n\t/users/login.php : /users/login.php:\n\t\tadmin:admin\n\t\tguest:guest",
"date_finished" : null,
"date_started" : null,
"detect_type" : "remote",
"false_positive" : false,
"has_notes" : true,
"hidden" : false,
"hide_from_now_on" : false,
"host_hidden" : false,
"host_id" : 31414753,
"hostname" : "172.20.71.98",
"id" : 1246848690,
"id_ddi" : 104433,
"ip_address" : "172.20.71.98",
"manually_added" : false,
"manually_added_fix_status_name" : null,
"matched_status" : "recurred",
"port" : 81,
"protocol" : "http",
"scan_block_id" : "197914",
"scan_id" : "102586",
"scanner_version" : "3.0.2.1",
"severities" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
},
"tag_list" : [
{
"codename" : "moderate to fix",
"color" : null,
"id" : 2304,
"name" : "moderate to fix",
"tagged_by" : "system"
},
{
"codename" : "web",
"color" : null,
"id" : 2303,
"name" : "web",
"tagged_by" : "system"
}
],
"title" : "HTTP Easily Guessable Credentials",
"transport" : "tcp",
"tunnel" : "none",
"vuln_class" : "explicit"
}
]
}Returns the notes assigned to a vulnerability given the <host_id> and vulnerability <id>.
GET https://vm.frontline.cloud/api/scanresults/active/hosts/<host_id>/vulnerabilities/<id>/notes/
$ curl https://vm.frontline.cloud/api/scanresults/active/hosts/31414753/vulnerabilities/1235054/notes/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
[
{
"account_user_account_id" : 1,
"account_user_email" : "barney.rubble@flintstone.com",
"account_user_id" : 260,
"account_user_name" : "Barney Rubble",
"date_created" : "2018-04-09T21:21:13.237611Z",
"date_modified" : "2018-04-09T21:21:13.237650Z",
"host_id" : 31414753,
"id" : 1235054,
"id_ddi" : 104433,
"note_group_id" : 1235054,
"note_original_author" : {
"account_user_email" : "barney.rubble@flintstone.com",
"account_user_fullname" : "Barney Rubble",
"account_user_id" : 260
},
"note_type" : "analyst",
"note_type_name" : "Analyst",
"order_number" : 0,
"scan_id" : "102586",
"scan_name" : "Scan Mar 27, 2018 3:38PM Don Test",
"scan_vulnerability_id" : 1246848690,
"target" : {
"data" : {
"title" : "HTTP Easily Guessable Credentials"
},
"type" : "vulnerability"
},
"ticket_metadata" : null,
"title" : null,
"value" : "Pass on to Network Team Alpha to address.",
"version" : 1
}
]Scan activity
Use these API paths to get information about current scan activity.
Returns a list of all active scans.
Available sort parameters
| Parameter | Description |
|---|---|
| asset_count | Sort list by the total number of assets scanned. |
| businessgroup_name | Sort list by business group. |
| date_finished | Sort list by the date the scan finished. |
| date_started | Sort list by the date the scan started. |
| name | Sort list by scan name. |
| scan_locations | Sort the list by external / internal scan location. |
| status | Sort list by scan status. |
| workflow | Sort list by the scan work-flow. |
Required parameters
| Parameter | Description |
|---|---|
| 0_in_scan_workflow | Set to one or more of the following: NOTE: You musts apply all to retrieve results that match the FVM Scan Activity page. |
| status | Set to one or more of the following: launching, paused, pausing, blackout, queued, resuming, running, loading, canceling, canceled, completed, errored, pt_in_progress, pt_review, pt_complete, waa_workflow.
NOTE: You must apply all to retrieve results that match the FVM Scan Activity page.
|
GET https://vm.frontline.cloud/api/scans/
$ curl https://vm.frontline.cloud/api/scans/?_0_in_scan_workflow=Penetration+Test%7CVulnerability+Assessment%7CWeb+Application+Assessment%7CThreat+Scan%7CPCI+Assessment+Follow-up%7CPCI+Assessment%7CPenetration+Test+Follow-up&count=2&ordering=-scan_locations,name,-date_finished&page=1&status=launching%7Cpaused%7Cpausing%7Cblackout%7Cqueued%7Cresuming%7Crunning%7Cloading%7Ccanceling%7Ccanceled%7Ccompleted%7Cerrored%7Cpt_in_progress%7Cpt_review%7Cpt_complete%7Cwaa_workflow \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 2996,
"next" : "https://vm.frontline.cloud/api/account/115/scans/?_0_in_scan_workflow=Penetration+Test%7CVulnerability+Assessment%7CWeb+Application+Assessment%7CThreat+Scan%7CPCI+Assessment+Follow-up%7CPCI+Assessment%7CPenetration+Test+Follow-up&count=25&ordering=-date_finished%2Cname&page=2&status=launching%7Cpaused%7Cpausing%7Cblackout%7Cqueued%7Cresuming%7Crunning%7Cloading%7Ccanceling%7Ccanceled%7Ccompleted%7Cerrored%7Cpt_in_progress%7Cpt_review%7Cpt_complete%7Cwaa_workflow",
"previous" : null,
"results" : [
{
"account" : {
"id" : 115,
"name" : "Demo Account"
},
"account_id" : 115,
"account_user" : "Administrator",
"account_user_id" : 34,
"build_reports" : false,
"businessgroups" : [
{
"id" : 540,
"name" : "Enterprise Admins"
}
],
"date_finished" : "2019-08-21T18:35:35.384192Z",
"date_modified" : "2019-08-21T18:35:35.582269Z",
"date_started" : "2019-08-21T18:01:24.682271Z",
"deleting" : false,
"description" : "",
"exclude_from_active_view" : false,
"force_target_detection" : false,,
"has_results" : false,
"host_count" : 51,
"id" : "97910_20190821T180000Z",
"name" : "Updated Weekly",
"next_event" : null,
"scan_locations" : "internal",
"scan_policy" : "Default",
"status" : "completed",
"status_message" : null,
"status_name" : "Completed",
"workflow" : "va_workflow"
},
...
]
}Returns the details for a specific scan <id> in the scan activity.
GET https://vm.frontline.cloud/api/scanresults/scans/<id>/
$ curl -X GET https://vm.frontline.cloud/api/scanresults/scans/97910_20190821T180000Z/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"active_view_version_id" : 348238,
"base_scan_id" : "97910_20190821T180000Z",
"businessgroups" : [
{
"id" : 540,
"name" : "Enterprise Admins"
},
]
"date_created" : "2019-08-21T18:01:24.682248Z",
"date_finished" : "2019-08-21T18:35:35.384192Z",
"date_modified" : "2019-08-21T18:35:35.582269Z",
"date_started" : "2019-08-21T18:01:24.682271Z",
"description" : "",
"exclude_from_active_view" : false,
"host_count" : 51,
"host_labels" : [],
"hosts_new_count" : 0,
"id" : "97910_20190821T180000Z",
"label_counts" : {},
"labels" : [],
"most_at_risk_hosts" : [
{
"active_view_cvss_score" : 10,
"active_view_date_created" : "2019-08-21T18:35:20.456496Z
"active_view_date_first_created" : "2015-10-02T17:18:30.216899Z",
"active_view_host_id" : 1978,
"active_view_host_rating_list" : {
"ddi" : "F",
"nvd" : "High",
"pci" : "Fail"
},
"active_view_risk_score" : 370,
"active_view_risk_weight" : 74,
"active_view_security_gpa" : 0,
"active_view_status" : "matched",
"active_view_system_security_gpa" : 0,},
"active_view_version" : 348238,
"active_view_security_gpa" : 0,
"active_view_vulnerability_count" : 57,
"active_view_vulnerability_severity_counts" : {
"unweighted" : {
"ddi" : {
"counts" : {
"critical" : 5,
"high" : 0,
"info" : 0,
"low" : 17,
"medium" : 22,
"none" : 0,
"trivial" : 35
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 1,
"low" : 26,
"medium" : 30
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 1,
"pass" : 56
},
"overall_security_gpa" : 0,
}
},
"weighted" : {
...
}
},
"assessed_cis_auth" : false,
"assessed_db_auth" : false,
"assessed_os_auth" : false,
"assessed_threatscan_auth" : false,
"assessed_unauth" : true,
"associated_webapps" : [],
"auth_status" : {
"details" : {},
"extended_details" : {},
"cis" : null,
"db" : {
"mssql" : null,
"mysql" : null,
"oracle" : null,
"postgresql" : null,
}
"os" : {
"linux" : null,
"vmware" : null,
"windows" : null
}
"threatscan" : null
}
"overall" : "N/A"
}
"aws_instance_id" : null,
"base_scan_id" : "97910_20190821T180000Z",
"date_finished" : null,
"date_started" : null,
"discovery_method" : "ping",
"dns_name" : "",
"dns_smartname" : "BUFF-HEARTBLEED",
"has_antivirus" : null,
"has_crimewareable" : null,
"has_disabled_antivirus" : null,
"has_exploitable" : true,
"has_malware" : null,
"has_notes" : false,
"has_outdated_antivirus" : null,
"hidden" : false,
"hide_from_now_on" : false,
"hostname" : "BUFF-HEARTBLEED",
"id" : 60688848,
"internal" : true,
"ip_address" : "192.168.69.140",
"is_compromised" : false,
"is_retired" : false,
"last_scanned_businessgroup" : {
"id" : 540,
"name" : "Enterprise Admins"
"mac_address" : "00:50:56:8d:bf:ba",
"matched_status" : "matched",
"named_asset_name" : null,
"netbios_name" : "BUFF-HEARTBLEED",
"netbios_smartname" : "BUFF-HEARTBLEED","
"network_profile_id" : 3488,
"network_profile_name" : "Internal Scanner Profile 4",
"notes_distribution" : {"id" : 540,
"asset" : false,
"asset_only" : false,
"vuln_only" : false
},
"os" : "Ubuntu Linux",
"os_family" : "unix",
"os_type" : "server",
"partially_scanned" : false,
"pentest_status" : null,{
"scan_block_id" : "385187_20190821T180000Z",
"scan_id" : "97910_20190821T180000Z",
"scan_version" : 704088,
"scan_version_active" : true,
"scan_version_cvss_score" : 10,
"scan_version_date_created" : "2019-08-21T18:35:20.456496Z",
"scan_version_host_id" : 60688848,
"scan_version_host_rating_list" : {
"ddi" : "F",
"nvd" : "High",
"pci" : "Fail"
},
"scan_version_risk_score" : 370,
"scan_version_risk_weight" : 74,
"scan_version_security_gpa" : 0,
"scan_version_system_security_gpa" : 0,
"scan_version_vulnerability_count" : 149,
"scan_version_vulnerability_severity_counts" : {
"unweighted" : {
"ddi" : {
"counts" : {
"critical" : 5,
"high" : 0,
"info" : 92,
"low" : 17,
"medium" : 0,
"none" : 0,
"trivial" : 35,
},
"overall_security_gpa" : 0
},
"nvd" : {
"counts" : {
"high" : 1,
"low" : 118,
"medium" : 30
},
"overall_security_gpa" : 0
},
"pci" : {
"counts" : {
"fail" : 1,
"pass" : 148
},
"overall_security_gpa" : 0
}
"weighted" : {
...
}
},
"scanner_version" : "3.0.36.1"
},
...
},
"most_common_malware" : [],
"most_common_vulnerabilities" : [
{
"hidden" : false,
"id_ddi" : 104120,
"matched_change" : {
"change" : 0,
"current" : 8,
"diff" : 8,
"fixed" : 0,
"new" : 0,
"recurred" : 8
},
"scan_vulnerability_count" : 8,
"severities" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
},
"title" : "Easily Guessable SSH Credentials",
"vuln_class" : "explicit"
},
...
},
"most_vulnerabilities_on_a_host" : 149,
"name" : "Updated Weekly",
"notifications" : [],
"os_counts" : {
"CentOS" : 2,
"Debian Linux" : 2,
...
},
"os_type_counts" : {
"client" : 8,
}
"pentest_date_completed" : null,
"pentest_date_started" : null,
"pentest_rating_list" : {
"ddi" : "D",
"nvd" : "High",
"pci" : "Not Compliant",
},
"previous_scan" : {
"businessgroups" : [
{
"id" : 540,
"name" : "Enterprise Admins"
}
],
"date_created" : "2019-08-14T18:02:38.093733Z",
"date_finished" : "2019-08-14T18:33:38.425841Z",
"date_modified" : "2019-08-14T18:33:38.619703Z",
"date_started" : "2019-08-14T18:02:38.093769Z",
"description" : "",
"host_count" : 51,
"id" : "97910_20190814T180000Z",
"name" : "Updated Weekly",
"pentest_date_completed" : null,
"pentest_date_started" : null,
"pentest_rating_list" : {
"ddi" : "D",
"nvd" : "High",
"pci" : "Not Compliant"
},
"scan_id" : "97910_20190814T180000Z",
"scan_policy" : {
"id" : 8,
"name" : "Default"
},
"scan_template" : {
"id" : 97910,
"name" : "Updated Weekly"
},
"security_gpa" : 0.95,
"status" : "completed",
"status_details" : [
[
"completed",
"Internal Scanner Profile 4",
"Successfully completed scan""
]
],
"status_message" : null,
"status_name" : "Completed",
"vulnerability_count" : 334,
"workflow" : {
"codename" : "va_workflow",
"id" : 2,
"name" : "Vulnerability Assessment"
},
}
"recent_recurring_scans" : [
{
"businessgroups" : [
{
"id" : 540,[
"name" : "Enterprise Admins"[
}
]
"date_created" : "2019-08-14T18:02:38.093733Z",
"date_finished" : "2019-08-14T18:33:38.425841Z",
date_modified" : "2019-08-14T18:33:38.619703Z",
"date_started" : "2019-08-14T18:02:38.093769Z",
"description" : "",
"id" : "97910_20190814T180000Z",
"name" : "Updated Weekly",
"pentest_date_completed" : null,
"pentest_date_started" : null,
"pentest_rating_list" : {
"ddi" : "D",
"nvd" : "High",
"pci" : "Not Compliant"
},
"scan_id" : "97910_20190814T180000Z",
"scan_policy" : {
"id" : 8,
"name" : "Default"
},
"scan_template" : {
"id" : 97910,
"name" : "Updated Weekly"
},
"status" : "completed",
"status_details" : [
[
"completed",
"Internal Scanner Profile 4",
"Successfully completed scan"
]
],
"status_message" : null,
"status_name" : "Completed",
"workflow" : {
"codename" : "va_workflow",
"id" : 2,
"name" : "Vulnerability Assessment"
}
},
...
},
"scan_id" : "97910_20190821T180000Z",
"scan_policy" : {
"id" : 8,
"name" : "Default"
},
"scan_rating_list" : {
"ddi" : "D",
..."nvd" : "High",
"pci" : "Not Compliant"
},
"scan_template" : {
"id" : 97910,
"name" : "Updated Weekly"
},
"security_gpa" : 0.95,
"security_gpa_external" : 0,
"security_gpa_internal" : 0.95,
"security_gpa_letter_external" : "F",
"security_gpa_letter_internal" : "D",
"status" : "completed",
"status_details" : [
[
"completed",
"Internal Scanner Profile 4",
"Successfully completed scan"
]
],
"status_message" : null,
"status_name" : "Completed",
"vuln_labels" : [],
"vulnerability_count" : 335,
"vulnerability_severity_counts" : {,
"unweighted" :
"ddi" : {
"counts" : {
"critical" : 26,
"high" : 12"
"info" : 1227,
"low" : 103,
"medium" : 22,
"none" : 0,
"trivial" : 172
}
"distinct_counts" : {
"critical" : 8,
"high" : 8,
"info" : 83,
"low" : 25,
"medium" : 6,
"none" : 0,
"trivial" : 23
},
"distinct_total" : 153,
"overall_rating" : "",
"overall_security_gpa" : 0,
"overall_severity" : "",
"rating_sort_order" : 0,
"severity_score" : 0,
"severity_sort_order" : 0,
"total" : 1562
},
"nvd" : {
...
},
"pci" : {
...
}
}
"weighted" : {
...
}
},
"workflow" : {
"codename" : "va_workflow",
"id" : 2,
"name" : "Vulnerability Assessment"
}
}Returns the details for a specific scan’s <id> asset details in the scan activity.
Available sort parameters
| Parameter | Description |
|---|---|
| active_view_date_created | Sort list by when assets were last found (scanned). |
| active_view_date_first_created | Sort list by date assets were first found. |
| active_view_rating_ddi | Sort list by asset rating. |
| hidden | Sort list by if asset is hidden. |
| host_scan_version_risk_score | Sort list by asset risk score. |
| host_scan_version_risk_weight | Sort list by asset risk weight. |
| host_scan_version_severity_ddi | Sort list by asset severity. |
| hostname | Sort list by asset hostname. |
| ip_address | Sort list by the asset IP address. |
| is_compromised | Sort list by whether an asset is compromised or not. |
| os | Sort list by the asset operating system. |
| os_type | Sort list by asset operating system type. |
| host_partially_scanned | Sort list by if asset is only partially scanned. |
GET https://vm.frontline.cloud/api/scanresults/scans/<id>/hosts/
$ curl -X GET https://vm.frontline.cloud/api/scanresults/scans/97910_20190821T180000Z/vulnerabilities/?count=50&digest=true&includeAcceptableRisk=false&includeFixed=false&includeHidden=false&ordering=-severity_ddi,-scan_vulnerability_count,title&page=1 \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 51,
"next" :
"https://vm.frontline.cloud/api/account/115/scanresults/scans/97910_20190821T180000Z/vulnerabilities/?count=2&digest=true&includeAcceptableRisk=false&includeFixed=false&includeHidden=false&ordering=-severity_ddi%2C-scan_vulnerability_count%2Ctitle&page=2",
"previous" : null,
"results" : [
{
"cvss_score" : "7.5",
"hidden" : false,
"id_ddi" : 104120,
"matched_change" : {
"change" : 0,
"change" : 0,
"diff" : 8,
"fixed" : 0,
"new" : 0,
"recurred" : 8
}
"scan_vulnerability_count" : 8,
"severities" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
}
"title" : "Easily Guessable SSH Credentials",
"vuln_class" : "explicit"
},
...
]
}Returns the details for a specific scan’s <id> vulnerabilities details in the scan activity.
Available sort parameters
| Parameter | Description |
|---|---|
| scan_vulnerability_count | Sort list by the total number of vulnerability instances per vulnerability. |
| severity_ddi | Sort list by vulnerability severity. |
| title | Sort list by vulnerability title. |
GET https://vm.frontline.cloud/api/scanresults/scans/<id>/hosts/
$ curl -X GET https://vm.frontline.cloud/api/scanresults/scans/97910_20190821T180000Z/hosts/?count=50&includeAcceptableRisk=false&includeFixed=false&includeHidden=false&ordering=-rating_ddi,hostname&page=1 \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 182,
"next"
"https://vm.frontline.cloud/api/account/115/scanresults/scans/97910_20190821T180000Z/vulnerabilities/?count=2&digest=true&includeAcceptableRisk=false&includeFixed=false&includeHidden=false&ordering=-severity_ddi%2C-scan_vulnerability_count%2Ctitle&page=2",
"previous" : null,
"results" : [
{
"cvss_score" : "7.5",
"hidden" : false,
"id_ddi" : 104120,
"matched_change" : {
"change" : 0,
"change" : 0,
"diff" : 8,
"fixed" : 0,
"new" : 0,
"recurred" : 8
"cis" : null,
}
"scan_vulnerability_count" : 8,
"severities" : {
"ddi" : "critical",
"nvd" : "high",
"pci" : "fail"
}
"title" : "Easily Guessable SSH Credentials",
"vuln_class" : "explicit"
},
"info" : 14,
"low" : 0,
"medium" : 0,
"none" : 0,
"trivial" : 0
},
"overall_security_gpa" : 0
},
"nvd" : {
...
},
"pci" : {
...
"weighted" : {
"ddi" : {
...
},
"nvd" : {
...
},
pci" : {
...
}
}
},
"scanner_version" : "3.0.36.1"
},
...
]
}Scheduled scans
Use these API paths to get information about scans that are scheduled.
Returns a list of all scheduled scans.
Available sort parameters
| Parameter | Description |
|---|---|
| active | Sort list by scan enabled / disabled. |
| businessgroup_name | Sort list by business group. |
| name | Sort the list by scan name. |
| next_start_date | Sort the list by the next start date. |
Required parameters
| Parameter | Description |
|---|---|
| _0_has_next_event | Set to true or false. If default is false. NOTE: Must be set to true and used in conjunction with expandScans=parameter to retrieve results that match the Scheduled Scans page. |
| expandScans | Set to true or false. If default is false. NOTE: Must be set to false to retrieve results that match the Scheduled Scans page. |
GET https://vm.frontline.cloud/api/scans/
$ curl -X GET https://vm.frontline.cloud/api/scans/?_0_has_next_event=true&expandScans=false&ordering=next_start_date,name&page=1&count=25 \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 2,
"next" : null,
"previous" : null,
"results" : [
{
"account" : {
"id" : 115,
}
"account_id" : 115,
"account_user" : "Administrator",
"account_user_id" : 34,
"active" : true,
"build_reports" : false,
"businessgroups" : [
{
"id" : 540,
"name" : "Enterprise Admins"
}
]
"description" : "",
"exclude_from_active_view" : false,
"force_target_detection" : false,
"id" : "97910",
"name" : "Updated Weekly","description" : "",
"next_event" : {
"id" : "98030_20190828T180000Z",
"start_date" : "2019-08-28T18:00:00Z",
"status" : "scheduled",
"timezone" : "America/Chicago"
}
"recurring" : true,
"scan_policy" : "Default",
"status" : null,
"visible" : true
},
...
]
}Returns the details for a specific scan <id> in the scheduled scans.
GET https://vm.frontline.cloud/api/scans/<id>/
$ curl -X GET https://vm.frontline.cloud/api/scans/97910/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"account" : {
"id" : 115,
"name" : "Demo Account"
},
"account_id" : 115,
"active" : true,
"adhoc_named_asset_targets" : [],
"adhoc_targets" : [
{
"account_id" : 115,
"asset_group_id" : 254008,
"filter_rule" : null,
"id" : 1201601,
"inclusion" : "full",
"ip_address_range" : {
"cidr_block" : null,
"dhcp" : false,
"fragile" : false,
"high_ip_address" : "192.168.69.254",]
"high_ip_number" : 3232253438,
"id" : 1175262,
"internal" : true,
"ipv6" : false,
"low_ip_address" : "192.168.69.1",
"low_ip_number" : 3232253185
},
"network_profile_id" : 3488,,
"network_profile_name" : "Internal Scanner Profile 4",
"port_range" : null,
"rule_action" : "include",
"rule_scope" : "scan",
"use_default_weight" : true,
"weight" : null
},
]
"asset_filter" : {},
"asset_groups" : [],
"build_reports" : false,
"businessgroups" :,
{
"id" : 540,
"name" : "Enterprise Admins"
}
],
"description" : "",
"exclude_from_active_view" : false,
"force_target_detection" : false,
"id" : "97910",
"name" : "Updated Weekly",
"notify" : false,
"recipients" : [],
"scan_policy" : "Default",
"scan_speed" : "normal",
"schedule" : {
"end_date" : null,
"id" : 98030,
"occurrences" : 78,
"recurrence_rules" : [
"FREQ=WEEKLY;INTERVAL=1;BYDAY=We"
],
"recurring" : true,
"start_date" : "2018-02-28T19:00:00Z",
"timezone" : "America/Chicago"
},
"workflow" : "va_workflow"
}General scans
Use these API paths to automate the creation of scans.
To create a scan, the following name-value pairs, members, objects, or arrays, must be submitted as a JSON object.
As in Fortra VM, there are four methods, or any combination thereof, by which you can create a scan.
They are by: Asset Groups, Ad Hoc IPs Ports, Ad Hoc Dynamic Asset, and Ad Hoc Hostnames.
In addition to those four methods, there are other scan options that you can configure as well. The below tables will further explain these, as well as provide "barebone" JSON examples.
POST https://vm.frontline.cloud/api/scans/
$ curl https://vm.frontline.cloud/api/scans/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X POST
-H 'Content-Type: application/json;charset=utf-8' \
--data '{"adhoc_named_asset_targets":[],"adhoc_targets":[],"asset_filter":{},"asset_groups":[218621],"build_reports":false,"businessgroups":[{"id":540}],"description":"","exclude_from_active_view":false,"internal":false,"name":"Test Asset Group Servers Scan","notify":false,"recipients":[],"scan_policy":"Default","scan_speed":"normal","schedule":{"end_date":null,"id":null,"recurrence_rules":[],"recurring":false,"start_date":"2019-09-17T17:15:00.000Z","timezone":"America/Chicago"},"workflow":"va_workflow"} ' \
{
"id": "207614",
"account": {
"id": 115,
},
"account_user": "Barney Rubble",
"account_user_id": 7703,
"businessgroups": [
}
"id": 540,
"name": "Enterprise Admins"
}
}
"name": "Test Asset Group Servers Scan",
"description": "",
"scan_policy": "Default",
"scan_speed": "normal",
"schedule": {
"id": 211430,
"start_date": "2019-09-17T17:15:00Z",
"end_date": "2019-09-17T17:15:00Z",
"recurring": false,
"recurrence_rules": [],
"timezone": "America/Chicago",
"occurrences": 0
}
"workflow": "va_workflow",
"adhoc_targets": [],
"adhoc_named_asset_targets": [],
"active": true,
"exclude_from_active_view": false,
"force_target_detection": false,
"build_reports": false,
"asset_groups": [
218621
],
"asset_filter": {
},
"recipients": [],
"notify": false,
"account_id": 115
}See the System section of this guide to learn how to retrieve a list of asset group <id>s.
Parameters
| Parameter | Description |
|---|---|
| asset_groups | An array of comma-separated asset group IDs. If not used, set to an empty array: [].
For information on retrieving a list of asset groups, see Integrations. |
{
"asset_groups" : [
113146,
113154
],
"schedule" : {
"start_date" : "2019-09-25T14:35:35.000Z",
"timezone" : "America/Chicago"}
}
} To scan by Ad Hoc IPs Ports, an array named adhoc_targets containing one or more objects, each containing the below required name-value pairs must be included. If not used, set to an empty array: [].
| Name | Description |
|---|---|
| autoadd | Set to true to auto-add IPs to the scanner profile in case they are not in the scanner profile already, otherwise, set to false. |
| inclusion | A string value. Set to full. |
| ip_address_range (required) | An object containing the following name-value pairs: cidr_block, dhcp, high_ip_address, ipv6, low_ip_address, low_ip_number. |
| cidr_block | A member of ip_address_range, a string value containing a valid CIDR address |
| low_ip_address (required, unless using cidr_block) | A member of ip_address_range, a string value containing a valid IPv4 address. |
| low_ip_number | A member of ip_address_range, a number value containing the decimal equivalent of the low_ip_address. |
| high_ip_address | A member of ip_address_range, a string value containing a valid IPv4 address. |
| high_ip_number | A member of ip_address_range, a number value containing the decimal equivalent of the high_ip_address. |
| network_profile_id (required) | A number value that is the scanner profile <id> to be used for this scan. See the System section for details on retrieving the scanner profiles. |
| port_range | An object containing the following name-value pairs: low_number, high_number. NOTE: For single-port rules, only the low_number is required. |
| rule_action (required) | A string value that will cause the IP range and / or ports to be included or excluded from this scan. Must be one of the following: include, exclude. |
{
"adhoc_targets" : [
{
"autoadd" : true,
"ip_address_range" : {
"low_ip_address" : "192.168.1.1"
},
"rule_action" : "include"
},
{
"autoadd" : true,
"network_profile_id" : 8386,
"port_range" : {
"low_number" : 8080
}
],
"schedule" : {
"start_date" : "2019-09-25T15:40:56.000Z",
"timezone" : "America/Chicago"
} To scan by Ad Hoc Dynamic Assets, an object containing name-value pairs that have asset and vulnerability filters is required.
For the options available, see Integrations and Integrations.
If not used, set to an empty JSON object: {}.
Parameters
| Name | Description |
|---|---|
| asset_filter | Example:"asset_filter":{ "_0_contains_host_os":
|
{
"asset_filter" : {
"_0_contains_host_os" : "Windows",
"_1_iexact_host_os_type" : "server"
},
"schedule" : {
"start_date" : "2019-09-25T16:35:01.000Z",
"timezone" : "America/Chicago"
}
} To scan by Ad Hoc Hostnames, you must include an array named adhoc_targets containing one or more objects, each containing the required name-value pairs in the Parameters table below. If not used, set to an empty array: [].
Parameters
| Name | Description |
|---|---|
| inclusion | A string value. Set to full. |
| named_asset | An object containing the following name-value pairs: code, codename, name. |
| code (required) | A member of named_asset, a number value set to 0. |
| codename (required) | A member of named_asset, a string value set to DNS. |
| name (required) | A member of named_asset, a string value containing the hostname of the asset to scan. |
| network_profile_id (required) | A number value that is the scanner profile <id> to use for this scan. |
| port_range | An object containing the following name-value pairs: high_number, low_number. NOTE: For single-port rules, only low_number is required. |
| rule_action (required) | A string value that will cause the IP range and ports to include or exclude from the scan. Must be one of the following: include, exclude. |
Now that we have covered the scanning for methods, the following table will cover the remaining name-value pairs that will complete the JSON object.
Parameters
| Name | Description |
|---|---|
| build_reports | Set to true if you want an Executive Summary and a Vulnerability Details report automatically generated upon scan completion, otherwise, set to false. Default is false. |
| businessgroups (conditionally required, see Note) | An array containing a single JSON object that has the name-value pair of the business group "id" and its number value. NOTE: This is required only if you are using Business Groups, otherwise, set to an empty array: f. For information on retrieving a list of business groups, see Integrations |
| exclude_from_active_view | Set to true to exclude the scan results from reconciling into Active View, otherwise, set to false. Default is false. |
| name | A string value that specifies the name of the scan. Limited to 100 characters. Default is similar to the following format: Scan Wed Sep 25 2024 14:20:57 GMT+0000 (UTC). |
| notify | Set to true if you want to add recipients who do not receive automatic scan notifications, otherwise, set to false. Default is false. |
| recipients | An array of values consisting of the users’ email address with Fortra VM. NOTE: If notify is set to false, then set recipients to an empty array: []. |
| scan_policy | A string value that is the name of the scan policy to be used for this scan, normally Default. For information on retrieving a list of other scan policies, see Integrations. Default is Default. |
| scan_speed | A string value that selects the scan speed. Value must be one of the following: slow, normal, quick, fast, very fast. WARNING: Faster scan speeds require more processing resources. Use with caution. Default is normal. |
| schedule (required) | An object consisting of the following name-value pairs: start_date and timezone. |
| start_date (required) | A member of schedule, a string value that is the ISO 8601 date-time value of when the scan is to start. Format is YYYY-MM-DDThh:mm:ss.sssZ. |
| timezone (required) | A member of schedule, a string value that represents your timezone location. |
| workflow | A string value that sets the type of work-flow for this scan. Value must be one of the following:
Default is va_workflow. |
{
"adhoc_named_asset_targets" : [
{
"inclusion" : "full",
"named_asset" : {
"code" : 0,
"codename" : "DNS",
"name" : "wD4587oiewjw29eml.local"
},
"network_profile_id" : 8386,
"port_range" : {
"low_number" : 80
},
"rule_action" : "include"
},
{
"inclusion" : "full",
"named_asset" : {
"code" : 0,
"codename" : "DNS",
"name" : "wD4587oiewjw30eml.local"
},
"network_profile_id" : 8386,
"port_range" : {
"low_number" : 443 },
"rule_action" : "include"
},
]
"schedule" : {
"start_date" : "2019-09-25T17:11:38.000Z",
"timezone" : "America/Chicago"
}
} {
"adhoc_named_asset_targets" : [
"adhoc_targets" : [
{
"ip_address_range" : {
"cidr_block" : null,
"dhcp" : false,
"fragile" : false,
"high_ip_address" : "192.168.1.1",
"high_ip_number" : 3232235777,
"ipv6" : false,
"low_ip_address" : "192.168.1.1",
},
"network_profile_id" : 8386,
"port_range" : {
"low_number" : 80
},
"rule_action" : "include"
},
{
"ip_address_range" : {
"cidr_block" : null,
"dhcp" : false,
"fragile" : false,
"high_ip_address" : "192.168.1.21",
"high_ip_number" : 3232235797,
"ipv6" : false,
"low_ip_address" : "192.168.1.21",
},
"network_profile_id" : 8386,
"port_range" : {
"low_number" : 443
},
"network_profile_id" : 8386,
"port_range" : {
"low_number" : 443
},
"rule_action" : "include"
},
]
"asset_filter" : {
"_0_contains_host_os" : "Windows",
"_1_iexact_host_os_type" : "server"
},
"asset_groups" : [],
"build_reports" : false,
"exclude_from_active_view" : false,
"internal" : false,
"name" : "Test Scan 2019-09-25T10:02:28",
"notify" : true,
"recipients" : [
"rubbleb@flint.stone",
"flintstonef@flint.stone"
],
"scan_policy" : "Default",
"scan_speed" : "normal",
"schedule" : {
"start_date" : "2019-09-25T19:56:45.000Z",
"timezone" : "America/Chicago"
}
"workflow" : "va_workflow"
}Scan Policies
Use this API path to get information about Scan Policies.
Returns a list of all returns a list of all Scan Policies.
GET https://vm.frontline.cloud/api/scans/policies/
$ curl https://vm.frontline.cloud/api/scans/policies/?count=25&ordering=name&page=1 \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
[
"default_for_workflow" : null,
"description" : "Configures the scanner to perform basic application discovery. This policy should be used to achieve a greater understanding of the target network while still not running a full blown vulnerability scan. It's similar to a simple service discovery scan but performs additional application fingerprinting to identify specific applications such as Jetty, WebLogic, CuteFTP, and IIS. While you have not yet run a vulnerability scan to look for weakness which may be present in these applications, you do know what your environment looks like and can act accordingly. This is a reconnaissance only scan policy and does not include checks for rated vulnerabilities.",
"id" : 12,
"name" : "Application Discovery",
"system" : true
}
...
}Reports
Use these API paths to get information about report history.
Returns a list of all reports.
Available sort parameters
| Parameter | Description |
|---|---|
| account_user | Sort the list by report creator. |
| businessgroup | Sort the list by business group. |
| date_created | Sort the list by the date created. |
| report_file | Sort the list by the file type. |
| report_type | Sort the list by the report type. |
| report_status | Sort the list by the report status. |
| template_name | Sort the list by the template. |
| title | Sort list by the vulnerability title. |
GET https://vm.frontline.cloud/api/reports/
$ curl https://vm.frontline.cloud/api/reports/?count=25&ordering=-date_created&page=1 \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count": 224,
"next":
"https://vm.us.frontline.cloud/api/account/115/reports/?count=25&ordering=-date_created&page=2",
"previous": null,
"results": [
{
"id": 169436,
"title": "Active View - Vulnerabilities CSV Export",
"date_created": "2019-09-27T19:21:12.866415Z",
"window_datetime": "2019-09-27T13:25:56.754042Z",
"report_source": "active",
"report_status": "complete",
"scan_id": null,
"active_view_version_id": 360934,
"businessgroups": [
{
"name": "Enterprise Admins",
"id": 540
}
},
"account": "Demo Account",
"account_id": 115,
"account_user": "Barney Rubble",
"account_user_id": 259,
"template": "csv_export_vulnerabilities",
"template_name": "Vulnerabilities CSV Export",
"report_file": "reports/19456b1f4de6f6057220d0d955a35b06",
"report_file_size": 155662,
"report_type": "active_view",
"file_type": "zip",
"report_filter": null,
"include_hidden": false,
"include_acceptable_risk": false,
"include_fixed": false,
"rating_type": "ddi",
"include_info_vulns": false,
"show_settings_appendix": false,
"show_filters_appendix": false,
"show_ratings_appendix": false,
"show_vulndict_appendix": false,
"show_toc": false,
"show_services": false,
"show_sitemap": false,
"show_purpose": false,
"show_notes": false,
"limit_hosts": true,
"dynamic_host_rating": false,
"exclude_sla_vulns": false,
"report_filename": "/reports/None"
},
...
}
}Returns the report for a specific report <report_file> in the report history.
GET https://vm.frontline.cloud/reports/<report_file>/
$ curl https://vm.frontline.cloud/api/reports/19456b1f4de6f6057220d0d955a35b06/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
-o 'Active View - Vulnerabilities CSV Export.zip' \
-X GETVulnerability dictionary
Use these API paths to get information about known vulnerabilities.
Returns a list of all known vulnerabilities in the vulnerability dictionary.
Parameters
| Parameter | Description |
|---|---|
| id_ddi | Sort the list by FVM ID. |
| is_new | Sort the list by if the vulnerability check is new. |
| severity_ddi | Sort the list by vulnerability severity. |
| title | Sort the list by vulnerability title. |
| include_details | Use true or false. Default is false. Set to true to include the solution and description in the vulnerabilities list. |
| include_references | Use true or false. Default is false. Set to true to include external references in the vulnerabilities list. |
GET https://vm.frontline.cloud/api/vulndictionary/
$ curl https://vm.frontline.cloud/api/vulndictionary/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 24597,
"next" : "https://vm.frontline.cloud/api/vulndictionary/?count=2&page=2",
"previous" : null,
"results" : [
{
"date_created" : "2015-04-29T15:49:53.710789Z",
"id" : 1627,
"id_ddi" : 103653,
"is_new" : false,
"is_recent" : false,
"namespace" : "ddi",
"products" : [
"VM"
],
"severity_list" : {
"ddi" : "Medium",
"nvd" : "High",
"pci" : "Fail"
},
"summary" : {
"cves" : [
"CVE-2008-1620"
],
"cvss_score" : 7.5,
"cvss_vector" : "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"date_disclosed" : "2008-03-31T00:00:00Z",
"date_discovered" : "2008-03-31T00:00:00Z",
"owasp_category" : "",
"tag_list" : [
"easy to fix",
"file transfer"
],
"title" : "2X ThinClientServer 2XTFTPd Service Directory Traversal"
}
},
...
...
]
}Returns the details for a specific vulnerability <id_ddi> in the vulnerability dictionary.
GET https://vm.frontline.cloud/api/vulndictionary/<id_ddi>/
$ curl https://vm.frontline.cloud/api/vulndictionary/104433/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"date_created" : "2015-04-29T15:49:53.730998Z",
"details" : {
"solution_details" : {
"detail_type" : "solution_details",
"name" : "Solution Details",
"revision" : 0,
"sort_order" : 5,
"value" : "It is advised that the password of the account(s) listed in the data section be changed to something secure and complex.",
"vulnerability_id" : 2196
},
"vulnerability_details" : {
"detail_type" : "vulnerability_details",
"name" : "Vulnerability Details",
"revision" : 0,
"sort_order" : 0,
"value" : "The web application on the this host has accounts configured with default or weak passwords. Attackers can easily leverage this condition to gain complete access to the web application.",
"vulnerability_id" : 2196
}
},
"id" : 2196,
"id_ddi" : 104433,
"is_new" : false,
"is_recent" : false,
"namespace" : "ddi",
"products" : [
"VM",
"WAS"
],
"references" : [],
"severity_list" : {
"ddi" : "Critical",
"nvd" : "High",
"pci" : "Fail"
},
"summary" : {
"cves" : [],
"cvss_score" : 10,
"cvss_vector" : "AV:N/AC:L/Au:N/C:C/I:C/A:C",
"date_disclosed" : "2011-05-14T00:00:00Z",
"date_discovered" : "2011-05-14T00:00:00Z",
"owasp_category" : "",
"tag_list" : [
"moderate to fix"
],
"title" : "HTTP Easily Guessable Credentials"
}
}System
Use these API paths to get details about various system information related to your account.
Returns a list of all system and user created asset groups.
Available sort parameters
| Parameter | Description |
|---|---|
| name | Sort the list by asset group name. |
| is_dynamic | Sort the list by asset group type. |
| rule_count | Sort the list by asset group rule count. |
| weight | Sort list by asset group risk weight. |
GET https://vm.frontline.cloud/api/assetgroups/
$ curl https://vm.frontline.cloud/api/assetgroups/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
[
{
"businessgroups" : [
{
"id" : 540,
"name" : "Enterprise Admins"
}
]
"description" : null,
"group_id" : 64407,
"id" : 257996,
"is_dynamic" : false,
"is_enabled_for_scanning" : true,
"name" : "10.10.10.x-Test",
"network_profile_names" : [
"Internal Scanner Profile 2",
"Not In Use 2"
]
"rule_count" : 3,
"system" : false,
"tip" : true,
"use_as_tag" : true,
"use_default_weight" : true,
"weight" : null
},
...
}Returns a list of all system and user created business groups.
Available sort parameters
| Parameter | Description |
|---|---|
| name | Sort the list by business group name. |
| primary_contact | Sort the list by business group primary contact. |
| user_count | Sort the list by business group rule count. |
GET https://vm.frontline.cloud/api/businessgroups/
$ curl https://vm.frontline.cloud/api/businessgroups/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
[
{
"all_account_users" : true,
"all_enterprise" : true,
"all_rules" : true,
"all_scanners" : true,
"assetgroups" : [
1234
...
]
"description" : "Enterprise Admins Group",
"group_members" : [],
"id" : 540,
"name" : "Enterprise Admins",
"primary_contact" : 222,
"readonly" : false,
"rules" : [],
"scanners" : [
9999,
...
]
"system" : true,
"user_count" : 0
},
...
}Returns a list of all Scanner Profiles.
Available sort parameters
| Parameter | Description |
|---|---|
| name | Sort the list by Scanner Profile name. |
| rule_count | Sort the list by Scanner Profile rule count. |
GET https://vm.frontline.cloud/api/networkprofiles/
$ curl https://vm.frontline.cloud/api/networkprofiles/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
[
{
"description" : null,
"id" : 3846,
"internal" : true,
"name" : "Wanderloop",
"rule_count" : 3,
"scanner_ids" : [
3987
]
"scanner_names" : [
"Wanderloop-VMInt-0118"
],
"sync_blackout_window" : true,
"use_default_weight" : true,
"visible" : true,
"weight" : 0
},
]Returns a single Scanner Profile for the given <id>.
GET https://vm.frontline.cloud/api/networkprofiles/<id>/
$ curl https://vm.frontline.cloud/api/networkprofiles/3846/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"blackout_window" : {
"Friday" : [
false,
...
],
"Monday" : [
...
],
"Saturday" : [
...
],
...
"id" : 3846
},
"description" : null,
"id" : 3846,
"internal" : true,
"name" : "Wanderloop",
"rule_count" : 3,
"rules" : [
{
"account_id" : 115,
"account_name" : "Demo Account",
"asset_group_id" : null,
"filter_rule" : null,
"id" : 1225810,
"inclusion" : "none",
"ip_address_range" : {],
"cidr_block" : null,
"dhcp" : false,
"fragile" : false,
"high_ip_address" : "10.255.255.255",
"high_ip_number" : 184549375,
"id" : 1198498,
"internal" : true,
"ipv6" : false,
"low_ip_address" : "10.0.0.0",
"low_ip_number" : 167772160
},
"named_asset" : null,
"network_profile_id" : 3846,
"network_profile_name" : "Wanderloop",
"port_range" : null,
"rule_action" : "include",
"rule_scope" : "scanner",
"scanner" : "N/A",
"use_default_weight" : true,
"weight" : null
},
...
]
"scanner_ids" : [
3987
]
"scanner_names" : [
"Wanderloop-VMInt-0118"
],
"sync_blackout_window" : true,
"use_default_weight" : true,
"visible" : true,
"weight" : 0
}Returns a list of a Scanner Profile’s <id> rules.
GET https://vm.frontline.cloud/api/networkprofiles/<id>/
$ curl https://vm.frontline.cloud/api/networkprofiles/3846/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"count" : 3,
"next" : null,
"previous" : null,
"results" : [
{
"account_id" : 115,
"account_name" : "Demo Account",
"asset_group_id" : null,
"filter_rule" : null,
"id" : 1225810,
"inclusion" : "none",
"ip_address_range" : {,
"cidr_block" : null,
"dhcp" : false,
"fragile" : false,
"high_ip_address" : "10.255.255.255",
"high_ip_number" : 184549375,
"id" : 1198498,
"internal" : true,
"ipv6" : false,
"low_ip_address" : "10.0.0.0",
"low_ip_number" : 167772160
},
"named_asset" : null,
"network_profile_id" : 3846,
"network_profile_name" : "Wanderloop",
"port_range" : null,
"rule_action" : "include",
"rule_scope" : "scanner",
"use_default_weight" : true,
"weight" : null
},
...
]
}Scanner IPs
Use these API paths to get the IP address assigned to an RNA scanner.
Returns a scanner's node_id value. Use this value with the Get network_interfaces data path.
GET https://vm.us.frontline.cloud/api/account/<account_id>/scanners/<scanner_id>/
$ curl https://vm.us.frontline.cloud/api/account/13982/scanners/76485/ \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"id": 76485,
"cluster_manager": null,
"cluster_group_members": [],
"name": "Demo Data Scanner",
"description": null,
"node_id": 53678,
"hostname": "DemoDataRNA",
"status": "online",
"port": 26206,
"internal": true,
"active": true,
"network_profile_id": 603,
"timezone": "America/Chicago",
"scanner_type": "rna",
"nirv_scanner": true,
"webapp_scanner": true,
"account_name": "Demo Account",
"account_id": 13982,
"clustered": false,
"network_profile_name": "Internal Scanner Profile",
"private": false,
"resource_acls": {
"owner_orgs": [
10815
],
"accessor_orgs": [
10815
],
"owner_users": [],
"accessor_users": []
},
"resource_acls_details": {
"owner_orgs": [
{
"id": 10815,
"name": "Enterprise Admins"
}
],
"accessor_orgs": [
{
"id": 10815,
"name": "Enterprise Admins"
}
],
"owner_users": [],
"accessor_users": []
}
}Returns a scanner's IP address by using the node_id value retrieved from the Get node_ID value path.
GET https://vm.us.frontline.cloud/api/account/<account_id>/nodes/<node_id>/?accountonly=true
$ curl https://vm.us.frontline.cloud/api/account/13982/nodes/53678/?accountonly=true \
-k \
-H 'Authorization: Token YOUR_API_TOKEN' \
-X GET
{
"id": 53678,
"cluster_manager": null,
"is_clustered": false,
"clusterable": false,
"hostname": "DemoDataRNA",
"shared": false,
"ssh_port_forward": 26206,
"memory": "1.7 GB",
"nirv_scanner": true,
"webapp_scanner": true,
"gpg_public_key": "",
"private": false,
"internal": true,
"search_domains": "test.local",
"dns_servers": "127.0.0.1,10.1.1.1",
"node_type": "rna",
"model_name": "N1100",
"virtual": false,
"arch": "x32",
"node_status": "online",
"proxy_hostname": "proxy03",
"proxy_port": 32789,
"chassis": {
"description": "Rack Mount Chassis",
"product": "ProLiant DL160 G6",
"vendor": "HP",
"version": "13",
"serial": "MXQ9310402"
},
"network_interfaces": [
{
"name": "eth0",
"address": "192.168.1.1",
"netmask": "255.255.255.0",
"networkFamily": "ipv4"
},
{
"name": "lo",
"address": "10.0.0.1",
"netmask": "255.0.0.0",
"networkFamily": "ipv4"
}
],
"disk_partitions": [
{
"mountPoint": "/",
"percentageUsed": "7%",
"freeBytes": "966M",
"usedBytes": "63M",
"capacityBytes": "1.1G",
"device": "/dev/sda3"
},
{
"mountPoint": "/boot",
"percentageUsed": "20%",
"freeBytes": "99M",
"usedBytes": "24M",
"capacityBytes": "130M",
"device": "/dev/sda1"
},
{
"mountPoint": "/home",
"percentageUsed": "6%",
"freeBytes": "9.7G",
"usedBytes": "610M",
"capacityBytes": "11G",
"device": "/dev/sda9"
},
{
"mountPoint": "/opt",
"percentageUsed": "25%",
"freeBytes": "102M",
"usedBytes": "33M",
"capacityBytes": "134M",
"device": "/dev/sda7"
},
{
"mountPoint": "/tmp",
"percentageUsed": "13%",
"freeBytes": "227M",
"usedBytes": "33M",
"capacityBytes": "259M",
"device": "/dev/sda8"
},
{
"mountPoint": "/usr",
"percentageUsed": "7%",
"freeBytes": "3.8G",
"usedBytes": "277M",
"capacityBytes": "4.1G",
"device": "/dev/sda5"
},
{
"mountPoint": "/var",
"percentageUsed": "61%",
"freeBytes": "802M",
"usedBytes": "1.3G",
"capacityBytes": "2.1G",
"device": "/dev/sda6"
},
{
"mountPoint": "/storage",
"percentageUsed": "80%",
"freeBytes": "45G",
"usedBytes": "174G",
"capacityBytes": "230G",
"device": "/dev/sdb1"
}
],
"software_versions": [
{
"name": "sparks",
"version": "1.0.13"
},
{
"name": "authscans",
"version": "1.0.1"
},
{
"name": "scanner",
"version": "2.1.2.2"
},
{
"name": "sequest-base",
"version": "1.0.0"
},
{
"name": "fallback",
"version": "1.0.0"
},
{
"name": "package-manager",
"version": "1.0.0"
},
{
"name": "openssh",
"version": "1.0.3"
},
{
"name": "kernel",
"version": "1.0.7"
},
{
"name": "keyring",
"version": "1.0.0"
}
],
"accounts": [
{
"id": 13982,
"name": "Demo Account"
}
],
"scanners": [
{
"account_id": 13982,
"account_name": "Demo Account",
"id": 76485,
"name": "Demo Data Scanner"
}
],
"scanner_version": "2.1.2.2",
"webapp_scanner_version": null,
"date_last_updated": "2022-09-19T17:11:58.188200Z",
"date_last_offline": "2022-09-19T17:11:58.157543Z",
"date_last_online": "2022-09-19T17:11:58.157548Z",
"account_id": "1",
"account_name": "Fortra",
"cluster_group_members": [],
"scan_statuses": {
"vm": {
"pt_in_progress": 0,
"pt_review": 0,
"scheduled": 0,
"launching": 0,
"running": 0,
"resuming": 0,
"pausing": 0,
"paused": 0,
"loading": 0,
"completed": 0,
"canceling": 0,
"canceled": 0,
"errored": 0,
"skipped": 0,
"deleting": 0,
"blackout": 0,
"queued": 0,
"cr_in_progress": 0,
"cr_review": 0,
"cr_publishing": 0,
"pci_scoping": 0,
"pci_scanning_pending": 0,
"pci_scanning_active": 0,
"pci_analysis_review": 0,
"pci_analysis_remediation": 0,
"pci_documentation_review": 0,
"pci_documentation_3b": 0,
"pci_reporting_final": 0,
"pci_reporting_review": 0,
"pci_complete": 0,
"pci_reporting_preview": 0
},
"was": {
"pt_in_progress": 0,
"pt_review": 0,
"scheduled": 1,
"launching": 0,
"running": 0,
"resuming": 0,
"pausing": 0,
"paused": 0,
"loading": 0,
"completed": 0,
"canceling": 0,
"canceled": 0,
"errored": 0,
"skipped": 0,
"deleting": 0,
"blackout": 0,
"queued": 0,
"cr_in_progress": 0,
"cr_review": 0,
"cr_publishing": 0,
"pci_scoping": 0,
"pci_scanning_pending": 0,
"pci_scanning_active": 0,
"pci_analysis_review": 0,
"pci_analysis_remediation": 0,
"pci_documentation_review": 0,
"pci_documentation_3b": 0,
"pci_reporting_final": 0,
"pci_reporting_review": 0,
"pci_complete": 0,
"pci_reporting_preview": 0
}
},
"rna_keys_users_access": []
}Filters
Fortra VM API filters give you great flexibility in tailoring your result set.
When using filter parameters, each parameter must be prefixed with a count using the format of _x_operand_filter. Query strings from different parameter groups can all begin with 0 (zero).
For example, you are searching for servers with an asset rating of F:
&_0_iexact_host_os_type=server&_0_eq_host_rating_ddi=F
Filters from the same filter group must increment their count.
For example, you are searching for servers or devices:
&_0_iin_host_os_type=server&_1_iin_host_os_type=device
Additionally, when using more than one filter, the filters intersect (AND) the results. For example, you are searching for assets that are servers AND have an asset rating of D or worse:
&_0_iexact_host_os_type=server&_0_lte_host_rating_ddi=D
You can, however, use our special union (OR) operands within the same group to union (OR) the results. For example, you are searching for assets that are a server OR device AND have an asset rating of A:
&_0_iin_host_os_type=server&_1_iin_host_os_type=device&_0_eq_host_rating_ddi=A
Be mindful when using OR operands as they cannot be mixed with AND operands from the same group. This will result in an empty set. For example, look at the following query:
&_0_lte_vuln_severity_ddi=High&_1_iin_vuln_severity_ddi=Low
The above intent was to retrieve vulnerabilities with a severity worse than or equal to High AND with a severity equal to Low (OR). Again, this will result in an empty set!
To properly retrieve Critical, High, and Low vulnerabilities, use the following instead:
&_0_iin_vuln_severity_ddi=Critical&_1_iin_vuln_severity_ddi=High&_2_iin_vuln_severity_ddi=Low
All of our filter parameters use operands to specify the target data. The below list defines the purpose of each operand.
| Parameter | Description |
|---|---|
| eq, iexact | Returns data exactly matching the given value. Used to create ‘AND’ type result sets. |
| noteq, notiexact | Returns data that does not exactly matching the given value. Used to create ‘AND’ type result sets. |
| in, iin | Returns data exactly matching the given value. Used to create ‘OR’ type result sets. |
| notin, notiin | Returns data that does not exactly match the given value. Used to create ‘OR’ type result sets. |
| contains | Returns data that matches the partial given value. Used to create ‘AND’ type result sets. |
| notcontains | Returns data that does not match the partial value given. Used to create ‘AND’ type result sets. |
| inicontains | Returns data partially matching the given value. Used to create ‘OR’ type result sets. |
| notincontains | Returns data partially that does not match the partial given value. Used to create ‘OR’ type result sets. |
| lt | Returns data that is less than the integer/decimal value or before the DateTime value. |
| lte | Returns data that is less than or equal to the integer/decimal value or before or equal to the DateTime value. |
| gt | Returns data that is greater than the integer/decimal value or after the DateTime value. |
| gte | Returns data that is greater than or equal to the integer / decimal value or after or equal to the DateTime value. |
The following table contains the various parameters that you can use to filter your results within Active View assets.
| Parameter | Description |
|---|---|
| host_active_view_status | Filter the Active View results by Status in Active View. Type: String. Must be one of the following: new, matched Operands: iexact, notiexact, iin, notiin |
| host_assessed_db_auth | Filter the Active View results by Assessed DB auth. Type: Boolean. Operands: eq, noteq |
| host_assessed_os_auth | Filter the Active View results by Assessed OS auth. Type: Boolean. Operands: eq, noteq |
| host_assessed_threatscan_auth | Filter the Active View results by Assessed threat scan. Type: Boolean. Operands: eq, noteq |
| host_assessed_unauth | Filter the Active View results by Assessed unauth. Type: Boolean. Operands: eq, noteq |
| host_belongs_to_asset_group | Filter the Active View results by Belongs to asset group. Type: String. Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains. |
| host_date_created | Filter the Active View results by Asset scanned on. Type: Date. Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| host_date_first_created | Filter the Active View results by Asset first scanned on. Type: Date. Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| host_discovered_in_last | Filter the Active View results by Asset discovered in last. Type: String. Must be one of the following: day, week, month, three months, six months, year Operands: eq, noteq |
| host_discovery_method | Filter the Active View results by Discovery Method. Type: String. Must be one of the following: unknown, syn, ping, forced, broadcast, arp, dns, syn-ack, ipsec, snmp, ntp, nbname, udp Operands: iexact, notiexact, iin, notiin |
| host_dns_name | Filter the Active View results by DNS name. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin. |
| host_duplicate_hostname | Filter the Active View results by Same hostnames. Type: Boolean. Operands: eq, noteq Used to build "Or Does Not Contain" queries. |
| host_duplicate_ip | Filter the Active View results by Same IPs. Type: Boolean. Operands: eq, noteq |
| host_has_antivirus | Filter the Active View results by Has anti-virus. Type: Boolean. Operands: eq, noteq |
| host_has_host_notes | Filter the Active View results by Has asset notes. Type: Boolean. Operands: eq, noteq |
| host_has_malware | Filter the Active View results by Has malware. Type: Boolean. Operands: eq, noteq |
| host_has_notes | Filter the Active View results by Has notes. Type: Boolean. Operands: eq, noteq |
| host_has_outdated_antivirus | Filter the Active View results by Has outdated anti-virus. Type: Boolean. Operands: eq, noteq |
| host_has_vuln_notes | Filter the Active View results by Has vulnerability notes. Type: Boolean. Operands: eq, noteq |
| host_hidden | Filter the Active View results by Hidden. Type: Boolean. Operands: eq, noteq |
| host_hostname | Filter the Active View results by Hostname. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_id | Filter the Active View results by Asset ID. Type: Integer. Operands: eq, in, noteq, notin, lt, lte, gt, gte |
| host_internal | Filter the Active View results by Detected with scanner type. Type: String. Must be one of the following: internal, external Operands: iexact, notiexact, iin, notiin |
| host_ip_address | Filter the Active View results by IP address. Type: Ip. Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains, lt, lte, gt, gte |
| host_ip_address_list_ranges | Filter the Active View results by IP address lists. Type: Stringexact. Operands: eq |
| host_is_compromised | Filter the Active View results by Compromised during Pentest. Type: Boolean. Operands: eq, noteq |
| host_labels | Filter the Active View results by Label. Type: String. Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| host_last_scanned_with_policy | Filter the Active View results by Last scanned using scan policy. Type: String. Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| host_last_scanned_with_template | Filter the Active View results by Last scanned with scan name. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_mac_address | Filter the Active View results by MAC address. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_named_asset_name | Filter the Active View results by DNS named asset. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_netbios_name | Filter the Active View results by NetBIOS name. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_network_profile | Filter the Active View results by Detected in scanner profile. Type: String. Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| host_new | Filter the Active View results by Asset is new. Type: Boolean. Operands: eq, noteq |
| host_notes_author | Filter the Active View results by Note Author. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_notes_content | Filter the Active View results by Note Content. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_only_scanned_with_policy | Filter the Active View results by Scanned only using scan policy. Type: String. Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| host_os | Filter the Active View results by OS. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_os_type | Filter the Active View results by Type. Type: String. Must be one of the following: client, server, ip phone, domain controller, device, firewall, printer, unknown Operands: iexact, notiexact, iin, notiin |
| host_partially_scanned | Filter the Active View results by Partially scanned. Type: Boolean. Operands: eq, noteq |
| host_rating_ddi | Filter the Active View results by Rating. Type: Rating. Must be one of the following: A, B, C, D, F Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| host_risk_weight | Filter the Active View results by Risk weight. Type: Integer. Operands: eq, in, noteq, notin, lt, lte, gt, gte |
| host_scan_id | Filter the Active View results by Associated scan id. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_scanned_in_last | Filter the Active View results by Asset scanned in last. Type: String. Must be one of the following: day, week, month, three months, six months, year Operands: eq, noteq |
| host_scanned_with_policy | Filter the Active View results by Scanned using scan policy. Type: String. Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| host_scanned_with_template | Filter the Active View results by Scanned with scan name. Type: String. Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| host_using_named_asset_name | Filter the Active View results by Asset scanned by hostname. Type: Boolean. Operands: eq, noteq |
The following table contains the various parameters that you can use to filter your results within Active View vulnerabilities.
| Parameter | Description |
|---|---|
| vuln_acceptable_risk | Filter the results by Acceptable risk. Type: Boolean Operands: eq, noteq |
| vuln_active_view_date_first_created | Filter the results by Date first found. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vuln_active_view_status | Filter the results by Status in Active View. Type: String. Must be one of the following: new, recurred, fixed Operands: iexact, notiexact, iin, notiin |
| vuln_cvc_added_in_last | Filter the results by CVC added to scanner in last. Type: String. Must be one of the following: day, week, month, three months, six months, year Operands: eq, noteq |
| vuln_cvss_score | Filter the results by CVSS score. Type: Decimal Operands: eq, noteq, lt, lte, gt, gte |
| vuln_cvss_vector | Filter the results by CVSS vector. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vuln_cvss_vector_a | Filter the results by CVSS availability. Type: String. Must be one of the following: complete, partial, none Operands: iexact, notiexact, iin, notiin |
| vuln_cvss_vector_ac | Filter the results by CVSS access complexity. Type: String. Must be one of the following: high, medium, low Operands: iexact, notiexact, iin, notiin |
| vuln_cvss_vector_au | Filter the results by CVSS authentication. Type: String. Must be one of the following: none, single, multiple Operands: iexact, notiexact, iin, notiin |
| vuln_cvss_vector_av | Filter the results by CVSS access vector. Type: String. Must be one of the following: local, adjacent, network Operands: iexact, notiexact, iin, notiin |
| vuln_cvss_vector_c | Filter the results by CVSS confidentiality. Type: String. Must be one of the following: complete, partial, none Operands: iexact, notiexact, iin, notiin |
| vuln_cvss_vector_i | Filter the results by CVSS integrity. Type: String. Must be one of the following: complete, partial, none Operands: iexact, notiexact, iin, notiin |
| vuln_data | Filter the results by Data. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vuln_date_created | Filter the results by Date found. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vuln_date_cvc_added_to_scanner | Filter the results by Date CVC added to scanner. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vuln_date_fixed | Filter the results by Date fixed. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vuln_detect_type | Filter the results by Detect method. Type: String. Must be one of the following: auth, unauth Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
| vuln_dictionary_labels | Filter the results by Vuln dictionary label. Type: String. Must be one of the following: xss, web, easy to fix, file transfer, database, rce, sqli, difficult to fix, voip, dos, mail, bof, moderate to fix Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
| vuln_false_positive | Filter the results by False positive. Type: Boolean Operands: eq, noteq |
| vuln_first_found_in_last | Filter the results by First found in last. Type: String. Must be one of the following: day, week, month, three months, six months, year Operands: eq, noteq |
| vuln_fixed_in_last | Filter the results by Fixed in last. Type: String. Must be one of the following: day, week, month, three months, six months, year Operands: eq, noteq |
| vuln_found_in_last | Filter the results by Found in last. Type: String. Must be one of the following: day, week, month, three months, six months, year Operands: eq, noteq |
| vuln_has_notes | Filter the results by Has notes. Type: Boolean Operands: eq, noteq |
| vuln_hidden | Filter the results by Hidden. Type: Boolean Operands: eq, noteq |
| vuln_hide_from_now_on | Filter the results by Continuously hidden. Type: Boolean Operands: eq, noteq |
| vuln_id | Filter the results by Instance ID. Type: Integer Operands: eq, in, noteq, notin, lt, lte, gt, gte |
| vuln_id_ddi | Filter the results by FVM ID. Type: Integer Operands: eq, in, noteq, notin, lt, lte, gt, gte |
| vuln_internal | Filter the results by Detected with scanner type. Type: String. Must be one of the following: internal, external Operands: iexact, notiexact, iin, notiin |
| vuln_is_crimewareable | Filter the results by Used by threat actors. Type: String. Must be one of the following: True, False, Unknown Operands: eq, noteq, in, notin |
| vuln_is_exploitable | Filter the results by Exploitable. Type: String. Must be one of the following: True, False, Unknown Operands: eq, noteq, in, notin |
| vuln_labels | Filter the results by Label. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| vuln_manually_added_fix_status_name | Filter the results by Manually added fix status. Type: String. Must be one of the following: unattempted, attempted, confirmed, failed Operands: eq, noteq, in, notin |
| vuln_manually_added_fixed_by_email | Filter the results by Manually Added fixed by (email). Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vuln_manually_added_fixed_by_name | Filter the results by Manually Added fixed by name. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vuln_network_profile | Filter the results by Detected in scanner profile. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| vuln_notes_author | Filter the results by Note Author. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vuln_notes_content | Filter the results by Note Content. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vuln_port | Filter the results by Port. Type: Port Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vuln_protocol | Filter the results by Protocol. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vuln_severity_ddi | Filter the results by Severity (FVM). Type: Rating. Must be one of the following: Critical, High, Medium, Low, Trivial, Info Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vuln_sla_enabled | Filter the results by SLA filter enabled. Type: Boolean Operands: eq, noteq |
| vuln_title | Filter the results by Title. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vuln_transport | Filter the results by Service transport. Type: String. Must be one of the following: tcp, udp, icmp Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
| vuln_tunnel | Filter the results by Tunnel. Type: String. Must be one of the following: ssl, none Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
| vuln_vuln_class | Filter the results by Detect class. Type: String. Must be one of the following: explicit, potential, recon, malware, compliance Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
The following table contains the various parameters that can be used to filter your scan results.
| Parameter | Description |
|---|---|
| asset_group | Filter the results by Scanned asset groups. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| businessgroup_name | Filter the results by Business Group. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| created_by_user | Filter the results by Created by user. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| date_finished | Filter the results by Date finished. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| date_started | Filter the results by Date started. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| ip_address | Filter the results by Scanned IPs. Type: Ip Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains, lt, lte, gt, gte |
| name | Filter the results by Name. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| scan_exclude_from_active_view | Filter the results by Included in Active View. Type: Boolean Operands: eq, noteq |
| scan_host_id | Filter the results by Asset ID. Type: Integer Operands: eq, in, noteq, notin, lt, lte, gt, gte |
| scan_locations | Filter the results by Scan Location. Type: String. Must be one of the following: both, external, internal Operands: eq, noteq |
| scan_policy | Filter the results by Using scan policy. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| scan_schedule_recurring | Filter the results by Using recurring schedule. Type: Boolean Operands: eq, noteq |
| scan_status | Filter the results by Status. Type: String. Must be one of the following: Scheduled, Launching, Running, Resuming, Pausing, Paused, Blackout, Queued, Loading, PT in progress, PT review, PT complete, Completed, Canceling, Canceled, Errored Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
| scan_vulnerability_id | Filter the results by Vulnerability ID. Type: Integer Operands: eq, in, noteq, notin, lt, lte, gt, gte |
| scan_workflow | Filter the results by Using workflow. Type: String. Must be one of the following: Penetration Test, Vulnerability Assessment Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
The following table contains the various parameters that can be used to filter your scan results.
| Parameter | Description |
|---|---|
| asset_group | Filter the results by Scanned asset groups. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| businessgroup_name | Filter the results by Business Groups. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| description | Filter the results by Description. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| ip_address | Filter the results by Scanned IPs. Type: Ip Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains, lt, lte, gt, gte |
| name | Filter the results by Name. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| scan_policy | Filter the results by Using scan policy. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| scan_schedule_recurring | Filter the results by Using recurring schedule. Type: Boolean Operands: eq, noteq |
The following table contains the various parameters that can be used to filter your report results.
| Parameter | Description |
|---|---|
| report_account_user | Filter the results by Created by. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| report_businessgroup_name | Filter the results by Business Group. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| report_date_created | Filter the results by Date created. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| report_report_status | Filter the results by Status. Type: String. Must be one of the following: generating, complete Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
| report_scan_created_by_user | Filter the results by Scan created by. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| report_title | Filter the results by Title. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
The following table contains the various parameters that can be used to filter your vuln dictionary results.
| Parameter | Description |
|---|---|
| products | Filter the results by Product. Type: String. Must be one of the following: VM, WAS Operands: eq, noteq |
| scanner_version | Filter the results by Scanner Version. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vulnerability_auth_only | Filter the results by Auth only. Type: Boolean Operands: eq, noteq |
| vulnerability_cvss_score | Filter the results by CVSS Score. Type: Decimal Operands: eq, noteq, lt, lte, gt, gte |
| vulnerability_cvss_vector | Filter the results by CVSS Vector. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vulnerability_cvss_vector_a | Filter the results by CVSS availability. Type: String. Must be one of the following: local, adjacent, network Operands: iexact, notiexact, iin, notiin |
| vulnerability_cvss_vector_ac | Filter the results by CVSS access complexity. Type: String. Must be one of the following: high, medium, low Operands: iexact, notiexact, iin, notiin |
| vulnerability_cvss_vector_au | Filter the results by CVSS authentication. Type: String. Must be one of the following: none, single, multiple Operands: iexact, notiexact, iin, notiin |
| vulnerability_cvss_vector_av | Filter the results by CVSS access vector. Type: String. Must be one of the following: local, adjacent, network Operands: iexact, notiexact, iin, notiin |
| vulnerability_cvss_vector_c | Filter the results by CVSS confidentiality. Type: String. Must be one of the following: local, adjacent, network Operands: iexact, notiexact, iin, notiin |
| vulnerability_cvss_vector_i | Filter the results by CVSS integrity. Type: String. Must be one of the following: local, adjacent, network Operands: iexact, notiexact, iin, notiin |
| vulnerability_date_created | Filter the results by Date added to FVM. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vulnerability_date_disclosed | Filter the results by Date disclosed. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vulnerability_date_discovered | Filter the results by Date discovered. Type: Date Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vulnerability_detail | Filter the results by Vulnerability details. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vulnerability_has_known_detect_types | Filter the results by Has detect types. Type: String. Must be one of the following: remote, auth Operands: eq, noteq |
| vulnerability_has_known_vuln_classes | Filter the results by Has vuln classes. Type: String. Must be one of the following: explicit, recon, potential, compliance, malware Operands: eq, noteq |
| vulnerability_id_ddi | Filter the results by FVM ID. Type: Integer Operands: eq, in, noteq, notin, lt, lte, gt, gte |
| vulnerability_is_new | Filter the results by Is new. Type: Boolean Operands: eq, noteq |
| vulnerability_reference | Filter the results by Reference. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| vulnerability_severity_ddi | Filter the results by Severity (FVM). Type: Rating. Must be one of the following: Critical, High, Medium, Low, Trivial, Info Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| vulnerability_title | Filter the results by Title. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
The following table contains the various parameters that can be used to filter your asset group results.
| Parameter | Description |
|---|---|
| assetgroup_name | Filter the results by Name. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| assetgroup_system | Filter the results by System Asset Group. Type: Boolean Operands: eq, noteq |
| assetgroup_weight | Filter the results by Risk weight. Type: Integer Operands: eq, in, noteq, notin, lt, lte, gt, gte |
| businessgroup_name | Filter the results by Business Group. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| networkprofile_name | Filter the results by Associated scanner profile. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| rule_inclusion | Filter the results by Has rules of inclusion type. Type: String. Must be one of the following: full, partial, none, n/a Operands: iexact, notiexact, iin, notiin |
| rule_network_internal | Filter the results by Has non-routable IPs. Type: Boolean Operands: eq, noteq |
| rule_network_ip_address | Filter the results by Has IP addresses. Type: Ip Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains, lt, lte, gt, gte |
| rule_port_number | Filter the results by Has ports. Type: Port Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| rule_rule_action | Filter the results by Has rule type. Type: String. Must be one of the following: Include, Exclude Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
The following table contains the various parameters you can use to filter your business group results.
| Parameter | Description |
|---|---|
| businessgroup_account_users | Filter the results by Member. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| businessgroup_description | Filter the results by Description. Type: String Operands: contains, inicontains, notcontains, notincontains, iexact, notiexact, iin, notiin |
| businessgroup_name | Filter the results by Name. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| businessgroup_primary_contact | Filter the results by Primary contact. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| businessgroup_scanners | Filter the results by Associated scanner. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
The following table contains the various parameters that can be used to filter your scanner profile results.
| Parameter | Description |
|---|---|
| networkprofile_internal | Filter the results by Is internal. Type: Boolean Operands: eq, noteq |
| networkprofile_name | Filter the results by Name. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |
| rule_network_internal | Filter the results by Has non-routable IPs. Type: Boolean Operands: eq, noteq |
| rule_network_ip_address | Filter the results by Has IP addresses. Type: Ip Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains, lt, lte, gt, gte |
| rule_port_number | Filter the results by Has ports. Type: Port Operands: eq, iin, noteq, notiin, lt, lte, gt, gte |
| rule_rule_action | Filter the results by Has rule type. Type: String. Must be one of the following: Include, Exclude Operands: iexact, notiexact, contains, inicontains, notcontains, notincontains |
| scanner_name | Filter the results by Associated scanner. Type: String Operands: eq, iin, noteq, notiin, contains, inicontains, notcontains, notincontains |