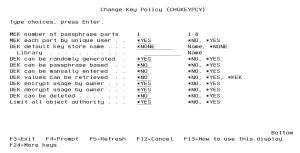
Change Key Policy (CHGKEYPCY)
The Change Key Policy (CHGKEYPCY) command allows you to specify the policy settings for the Symmetric Key Management System.
For details and recommended settings, see Configuring Key Policy Settings in Getting Started.
The following users can use this command:
- QSECOFR user profile (unless excluded in the Key Officer settings)
- A user profile with *SECADM authority (unless excluded in the Key Officer settings)
- A Key Officer that has a *YES specified for the “Maintain key policy and alerts” authority setting
How to Get There
From the Key Policy and Security Menu, choose option 1, Change Key Policy. Or, prompt (F4) the command CRYPTO/CHGKEYPCY.
Field Descriptions
MEK number of passphrase parts (MEKPRT)
Indicates the number of passphrase parts that must be entered (loaded) before a Master Encryption Key (MEK) can be generated (set).
MEK each part by unique user (MEKUNQUSR)
Indicates whether or not each MEK (Master Encryption Key) passphrase part must be entered (loaded) by a different user profile.
The possible values are:
DEK default key store name (DEKKEYSTR)
Indicates the object name and library of the default Key Store which contains the Data Encryption Keys (DEK).
The possible library values are:
DEK can be randomly generated (DEKRNDGEN)
Indicates whether a Data Encryption Key (DEK) can be randomly generated with the CRTSYMKEY (Create Symmetric Key) command.
The possible values are:
DEK can be passphrase based (DEKPASBSD)
Indicates whether a Data Encryption Key (DEK) can be generated with a user-entered passphrase with the CRTSYMKEY (Create Symmetric Key) command.
The possible values are:
DEK can be manually entered (DEKMANENT)
Indicates whether a Data Encryption Key (DEK) value can be manually entered with the CRTSYMKEY (Create Symmetric Key) command.
The possible values are:
DEK values can be retrieved (DEKRTVVAL)
Indicates whether Data Encryption Key (DEK) values can be retrieved with the EXPSYMKEY (Export Symmetric Key) command.
The possible values are:
DEK encrypt usage by owner (DEKENCOWN)
Indicates whether the user profile which created a Data Encryption Key (DEK) can use that DEK to encrypt data.
The possible values are:
DEK Decrypt usage by owner (DEKDECOWN)
Indicates whether the user profile which created a Data Encryption Key (DEK) can use that DEK to decrypt data.
The possible values are:
DEK can be deleted (DEKDLTALW)
Indicates whether a Data Encryption Key (DEK) can be deleted from a Key Store.
The possible values are:
Limit all-object authority (LMTALLOBJ)
Indicates whether to limit authority for users with *ALLOBJ special authority to Key Stores and Authorization Lists used in the Field Registry.
The possible values are: