For details of configuring Servers and Sites, and enabling ARM on EFT Server, refer to the following topics:
The wizard performs several checks and asks you to provide information or make changes based on the results of those checks, including:
The wizard is quite intuitive and provides instructions where necessary. The wizard pages change based on your selections. The procedure below walks you through the most common scenarios.
-
Do one of the following:
-
After Server setup is complete, the Site Setup wizard appears.
-
In the administration interface, click Configuration > New Site.
The Site Setup wizard Welcome page appears.
-
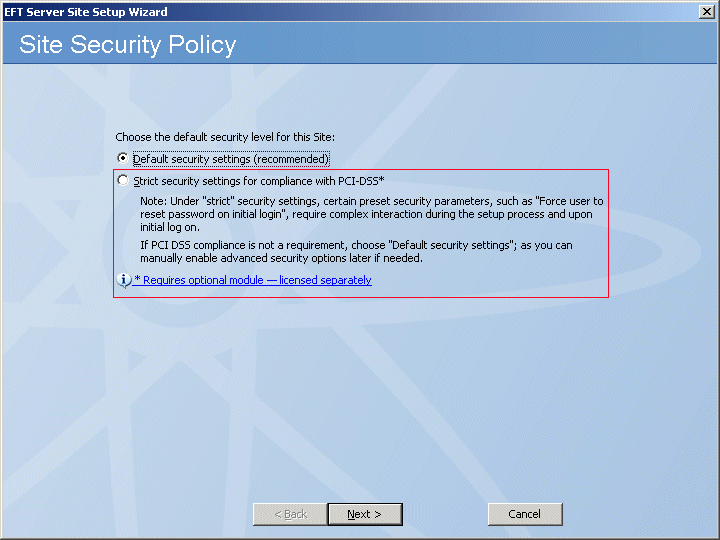
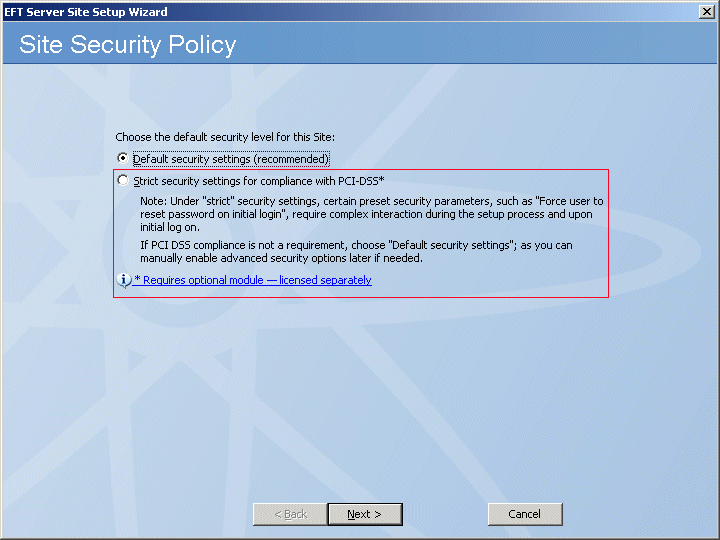
Click Strict security settings, then click Next. The Site name page appears.
-
In the Site name box, type a name a unique name for the Site. The default name is MySite, but you change it to anything you want. The name you provide here will appear in EFT Server tree in the left pane of the administration interface and in reports and messages.
-
In the Listening IP box, specify the IP address the Site should listen on, or leave the default of All Incoming.
-
Click Next. The Site Root Folder page appears.
-
In the Site root box, leave the default or click Browse to specify the root folder.
-
In the Additional site root folder options area, select or clear the check boxes as needed:
-
Select the Automatically create UNIX-style subfolders check box to create Usr, Pub, Bin, and Incoming folders with appropriate permissions under the root folder. This is only necessary if you are trying to mimic a typical default *nix Server setup.
-
Select the Automatically create and assign home folders to newly created users to create a user folder automatically under \Site Root\Usr\ when a new user is added.
-
Click Next. The User Authentication page appears.
-
In the Authentication type list, specify one of the following authentication methods that this Site will use to authenticate user connections:
|

|
When you create a PCI DSS Site that uses AD or LDAP authentication, the following states will not be audited for user accounts but will be audited for non-AD administrator accounts:
-
Password complexity and length requirements
-
Password history requirements
-
Password reset requirements
-
Password expiration requirements
-
Password anonymous requirements
-
Password e-mailing to user requirements
The same PCI DSS requirement checks are skipped when RADIUS or RSA SecurID is used, and compensating controls are shown in their place.
|
-
Click Next. The EFT Server Authentication page appears. The default path to store the user database appears in the box. If you want to store the user database in a different location, click the Browse icon or type the path in the box.
-
Click Next. The Perimeter Network Security page appears.
-
Specify whether to connect the Site to EFT Server's DMZ Gateway.
-
If you choose not to connect to DMZ Gateway or have not yet installed DMZ Gateway, click in the text box and provide a reason (compensating control) for not using DMZ Gateway. (The reason will appear in the Description box of the PCI DSS Compliance report.)
-
If you choose to connect to DMZ Gateway, click Connect this Site to DMZ Gateway Server, specify its IP address and port, then click Test Connection.
-
Click Next. If you specified a default port for DMZ Gateway, the Vendor Defaults page appears.
-
Change the port number to a non-default number, or provide a reason for keeping the default port. (The reason will appear in the Description box of the PCI DSS Compliance report.)
-
Click Next. If EFT Server was configured with the default Administrator port of 1100, the Vendor Defaults page appears for you to change the Administrator port or provide justification for using the default.
-
Click Next. The Data Retention and Disposal page appears.
-
Do one of the following:
-
Specify the file extensions to be deleted, the frequency, and the folder from which to delete them.
-
Click Don't set a data retention and disposal policy, then, in the text box, provide the justification and compensating control. (The reason will appear in the Description box of the PCI DSS Compliance report.) Refer to Specifying File Deletion Options for more data wiping options. You can always setup a clean-up policy later.
-
Click Next. The Administrator Account Password Security page appears.
-
Keep the default of enabling the administrator account password security settings or click Continue without changing administrator account password security settings, then provide the justification and compensating control. (The reason will appear in the Description box of the PCI DSS Compliance report.)
-
Click Next. The Daily PCI DSS Audit Report page appears.
-
Do one of the following:
-
Click Audit and send daily report, then provide the recipient's e-mail address. (The SMTP settings were configured during Server setup.)
-
Click Do not generate daily report and type a reason for not generating the report automatically. For example, you can manually generate the report as needed in the administration interface. (The reason will appear in the Description box of the PCI DSS Compliance report.)
-
Click Next. The Data Sanitization page appears.
-
Do one of the following:
-
Click Enable data wiping, then, in the Data sanitization method box, click which method EFT Server is to use to wipe data.
-
Click Windows default (no wipe) and type a reason for not specifying a data sanitization method for EFT Server to use. For example, you might be using a third-party tool for sanitization. (The reason will appear in the Description box of the PCI DSS Compliance report.)
-
Click Next. The Connection Protocols page appears.
-
Select one or more check boxes for the protocol(s) and specify the port numbers that this Site will use to connect to EFT Server.
|

|
If you specify plain-text FTP or HTTP, after you click Next, EFT Server will prompt you to disable these insecure protocols or continue and supply justification.
|
-
If you choose SSL, click SSL options and SSL certs for further configuration.
-
-
If you choose SFTP, click SFTP options and SFTP keys for further configuration. EFT Server will automatically generate SFTP keys if SFTP is selected.
-
|

|
Because the SFTP Public key only method does not use a password, it potentially violates the PCI DSS and is, therefore, not available with PCI DSS Sites. You can, however, use the Public Key and Password authentication method.
|
-
If you choose AS2 over HTTP/S, click Configure to specify your AS2 identifier and certificate information.
-
Click Next. If the default SFTP banner message is used on EFT Server, the Vendor Default warning page appears. Do one of the following:
-
Click Change SFTP message banner to, then provide the software version and, optionally, comments.
-
Click Continue without making any changes, then type the reason for keeping the default banner message.
-
Click Next. The Site Setup Completed page appears.
-
You are offered the option of continuing to the User Creation wizard or quitting the wizard. Click an option, then click Finish. The PCI DSS Site appears in the tree on the Server tab.
![]()